AOL Instant Messenger (often referred to as “AIM”) is an instant messaging application that allows registered users to communicate in real time via text, voice, and video transmission over the Internet. It is maintained by AOL LLC. The official website is www.aim.com.
AIM is widely used all over the world. However, employees are using AIM to chat privacy topics, send and receive files, which will decrease working productivity, waste time and raise security risk.
So it is important to block AIM in enterprise network.
How to block AIM in your network?
AIM messenger can connect in several ways. Default is TCP port 5190. However, if you block AIM port 5190 in your firewall. It will turn to use port 80, 443 instead. And also, AIM messenger can use a HTTP/SOCK4/SOCK5 proxy server to reach the server. Even the worth, AIM traffics through port 80 using HTTP protocol, if you allow your employees to browser website, the 80 port must be available. And AIM has official clients, and many unofficial clients like gaim, trillian are also popular.
So, is blocking AIM mission impossible?
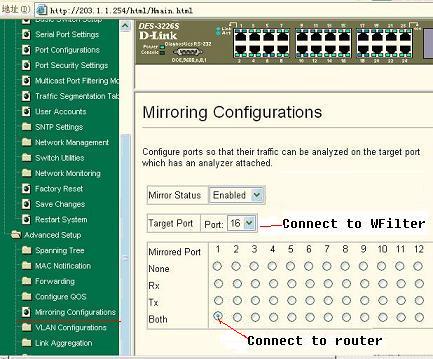
Of course not, but professional internet filter tools are needed. To block aim traffic, it needs the blocking aim tool has the ability to pick up aim traffic from large amount of connections.
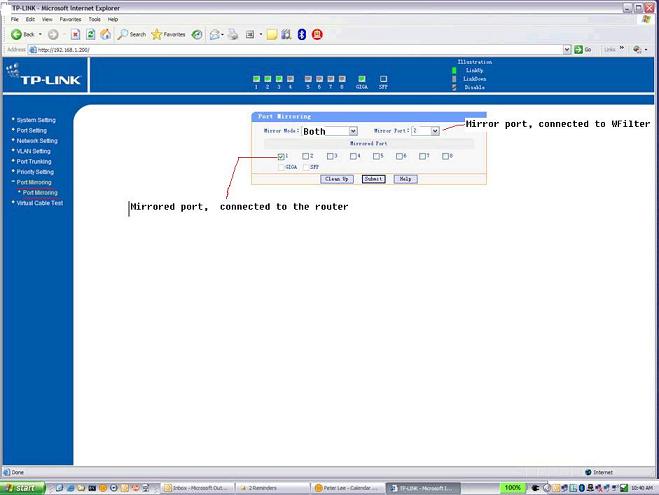
I recommend you use WFilter to block aim, block msn and block messenger.
WFilter related features:
- Monitor AIM and ICQ messenger usage.
- Record chat contents of AIM and ICQ.
- Record files transfered by AIM/ICQ.
- Implement a policy to block AIM/ICQ or certain AIM/ICQ accounts.
- Block AIM file transfers, block icq file transfers.
- Support offical messenger client and other third party clients like gaim, trillian.
WFilter other monitor features:
Chat Monitor, MSN Messenger Chat Monitor, Yahoo Chat Monitor and other instant messenger monitor, block MSN, block Yahoo, block AIM, and other instant messenger block, block p2p, block p2p traffic, filter internet, block internet, internet monitor, monitor employee internet activity…