You will come to the following solutions when your internet bandwidth is insufficient:
Actullay, these three solutions have disadvantages:
- 1. Without access control, using multiple broadband connections can not bring better experience. It because downloading and streaming can easily consume most of your bandwidth.
- 2. “Application blocking” can save your bandwidth. However, users experience are impacted. Users will complain about no streaming or downloading.
- 3. Rate limiting does not optimize your bandwidth. Users will still complain about slow internet speed.
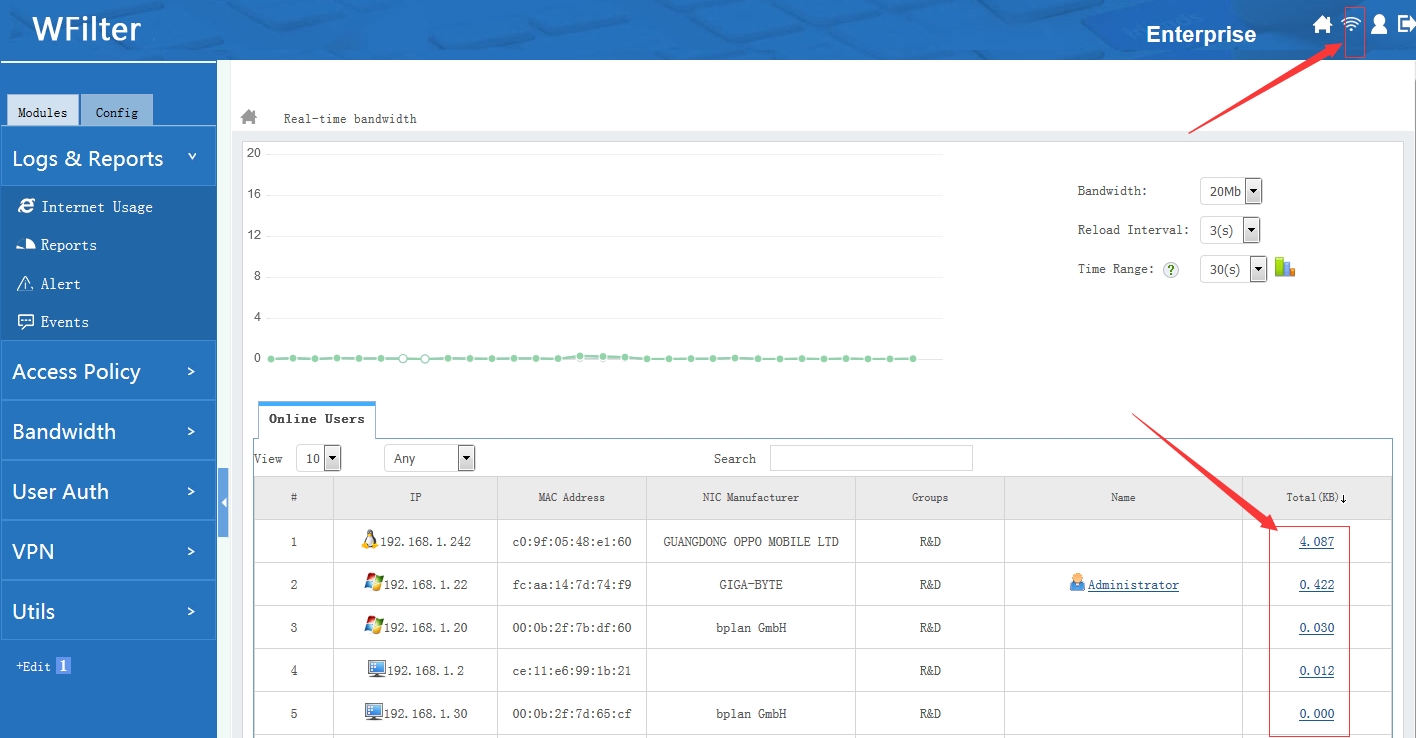
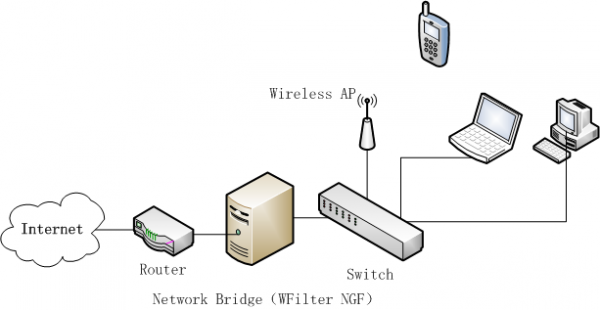
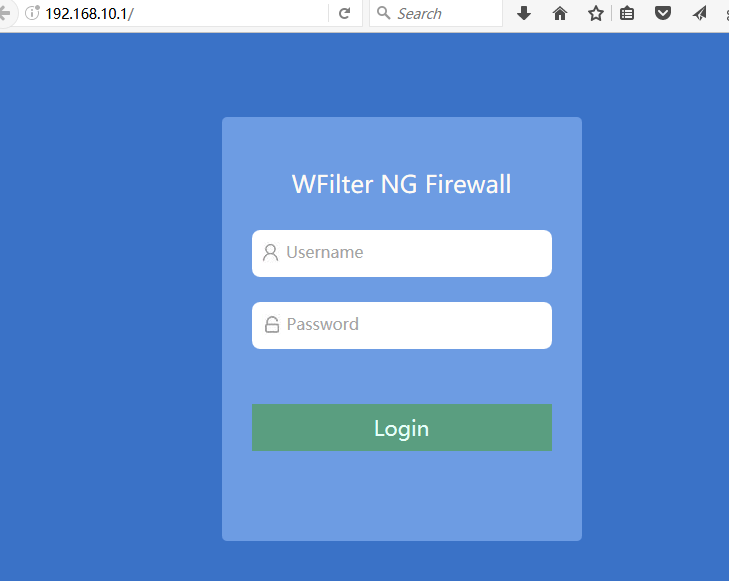
WFilter NG firewall brings a total solution for bandwidth optimization.
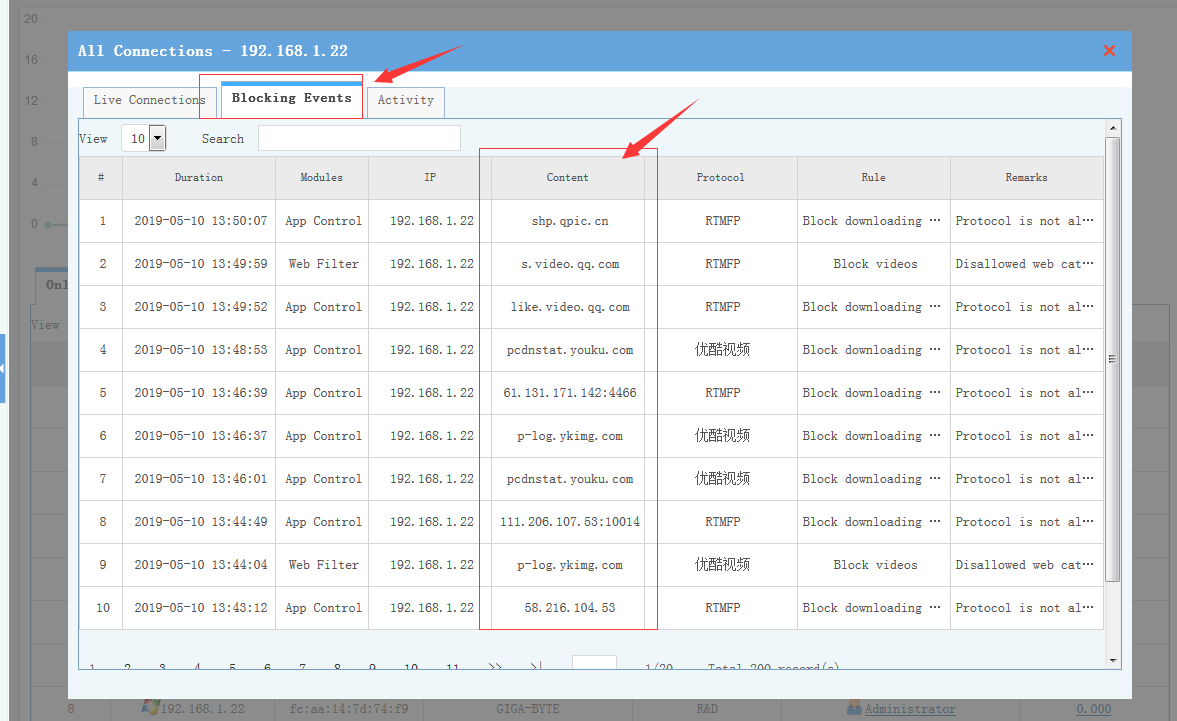
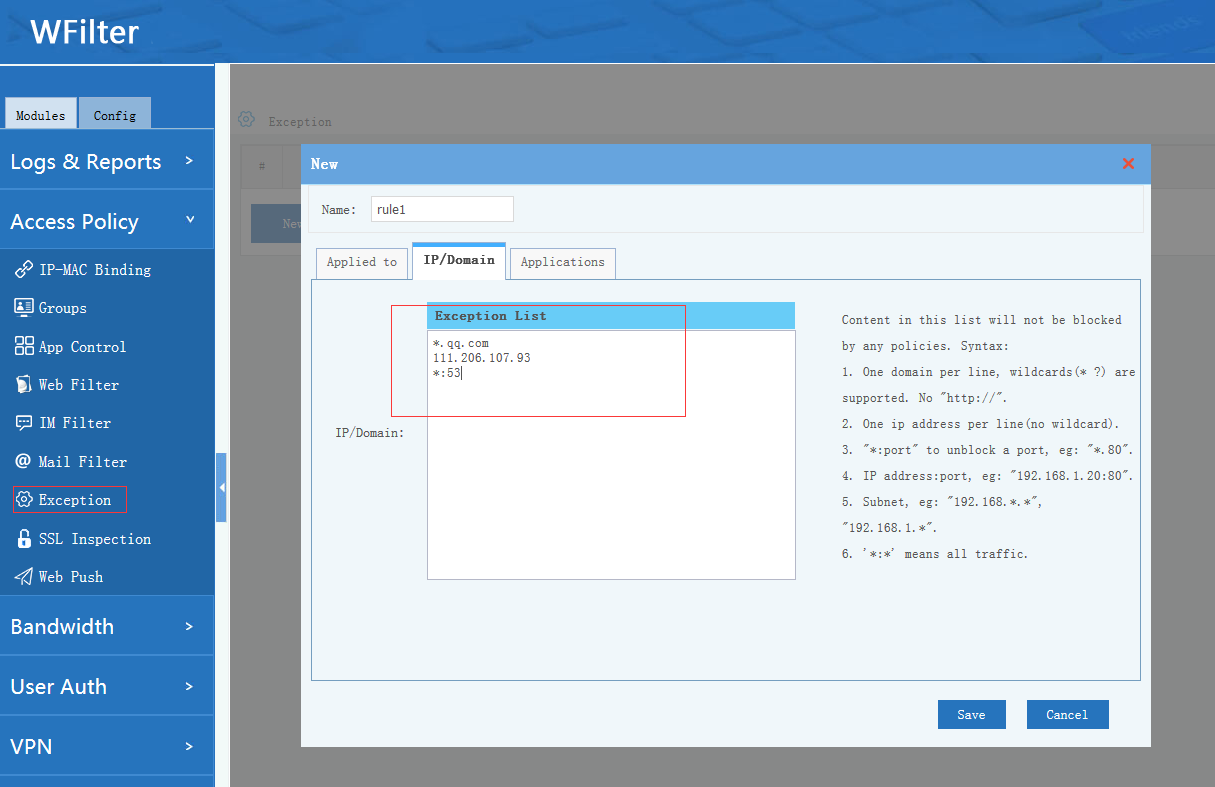
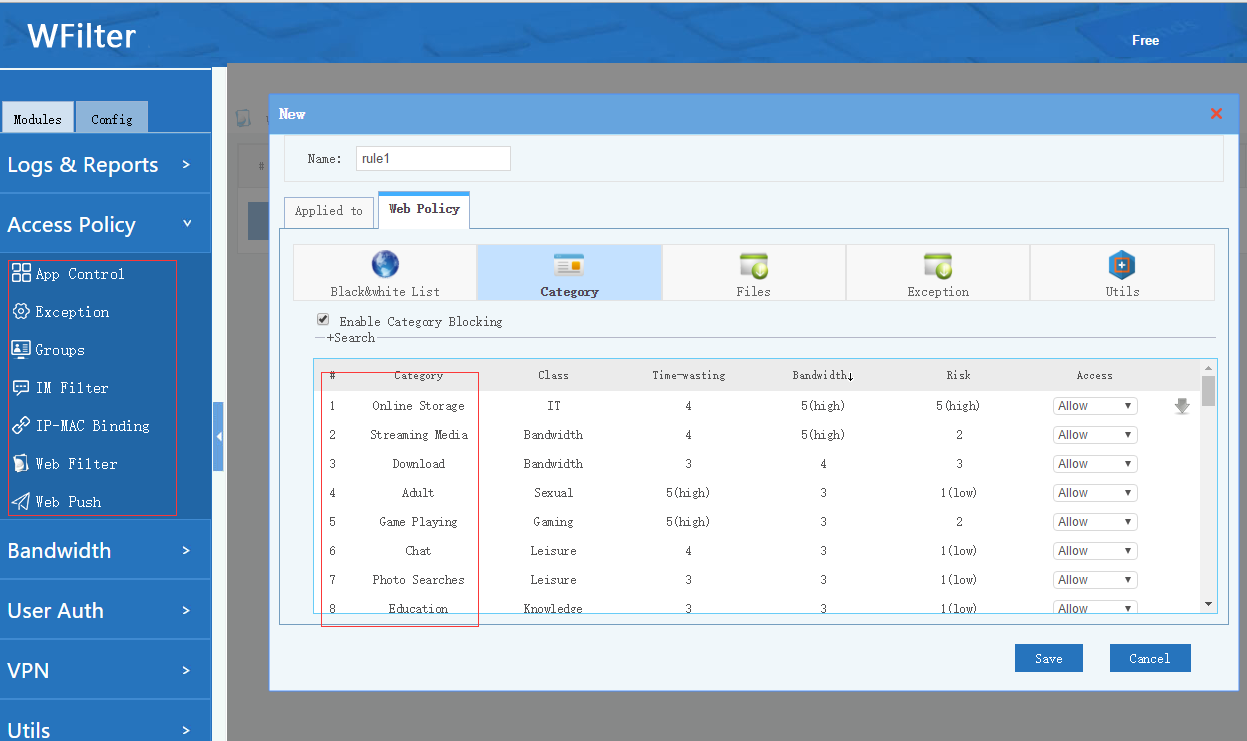
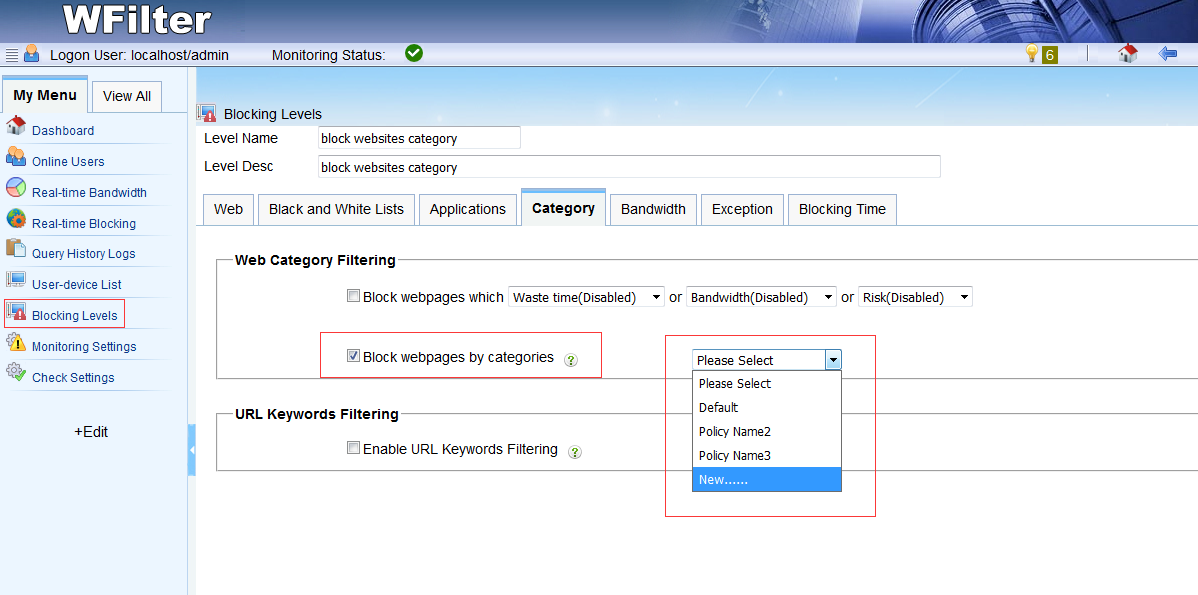
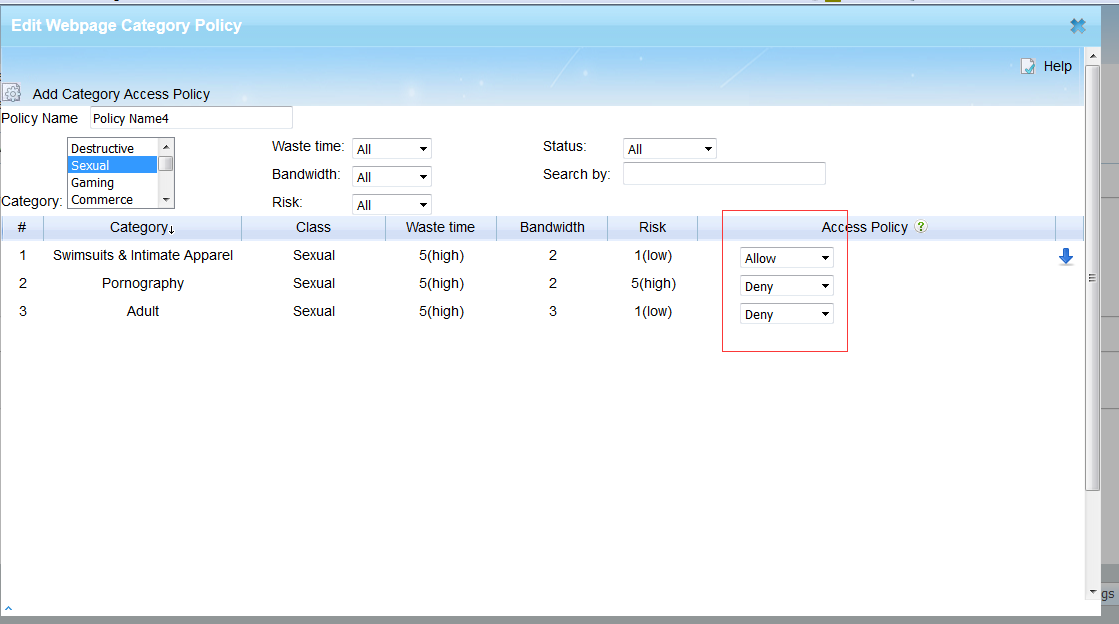
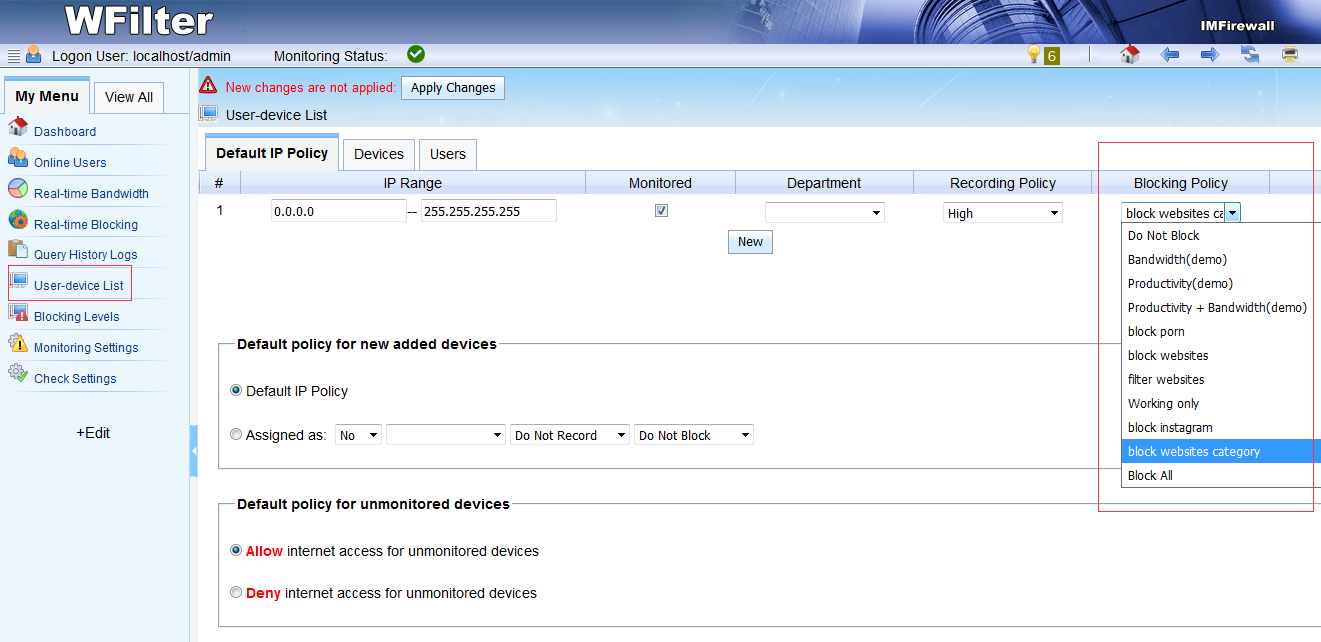
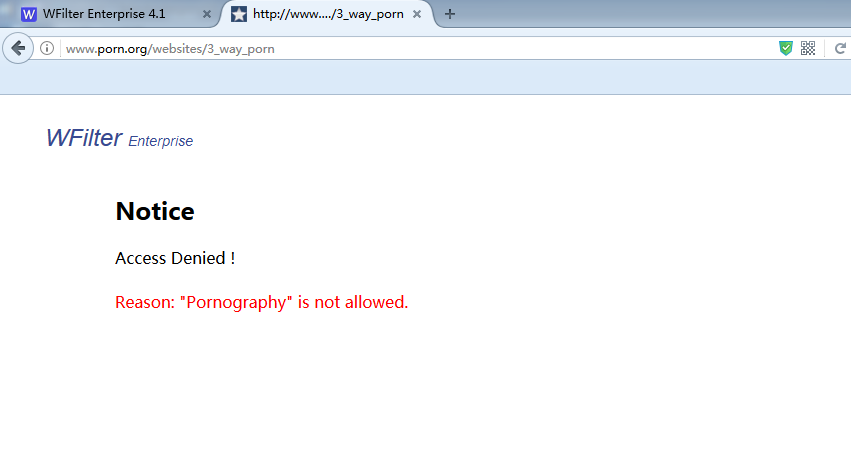
1. Powerful access control policy
With “Access Policy” modules, you can block p2p downloading, online streaming, streaming websites. Please check: Access Policy
2. Multi-WAN load balancing and routing
In case you have multiple broadband connections, WFilter NGF’s “Multi-WAN” module can help you to:
- 1. Load balancing on multiple broadband connections.
- 2. Setup routing policies. For example, a). business servers are routed to a dedicated connection, b). video sites are routed to another connection.
For more details, please check: Muti-WAN
3. Bandwidth priority
With the “Priority” module, traffic with higher priority goes first. For example, you can set business servers traffic to the highest priority. So even the network is extremly busy, servers bandwidth won’t be influenced.
When installed, there are default rules: email > web > p2p and streaming. You also can customize your own rules.
For more details, please check: bandwidth priority
4. Bandwidth shaper
This module is for you to set bandwidth rate for clients. You can set the rate to ip ranges, user group or department.
Each group have a “maximum bandwidth rate” and “minimum bandwidth rate”. The minimum rate ensures the clients to have this bandwidth rate even the line is busy.
For more details, please check: bandwidth shaper
Try WFilter NGF now: WFilter NG firewall