Traffic Shaping and Prioritization is becoming more and more common in the corporate market. Most companies with remote offices are now connected via a WAN (Wide Area Network). Applications tend to become centrally hosted at the head office and remote offices are expected to pull data from central databases and server farms. As applications become more hungry in terms of bandwidth and prices of dedicated circuits being relatively high in most areas of the world, instead of increasing the size of their WAN circuits, companies feel the need to properly manage their circuits to make sure business-oriented traffic gets priority over best-effort traffic. Traffic shaping is thus a good means for companies to avoid purchasing additional bandwidth while properly managing these resources.
With a linux gateway, you have a very rich set of tools for managing and manipulating the transmission of packets. More details can be found at: http://linux-ip.net/articles/Traffic-Control-HOWTO/index.html, However, sometimes it might be difficult for you to deploy a linux gateway server.
This tutorial will guide to implement a passby bandwidth management solution, which enables you to manage internet bandwidth through a mirroring port on your switch. Port mirroring allows you to setup a port in the switch to receive packets of other ports. Setting up a mirror port does no change to your network topology, and it will not affect your network speed.
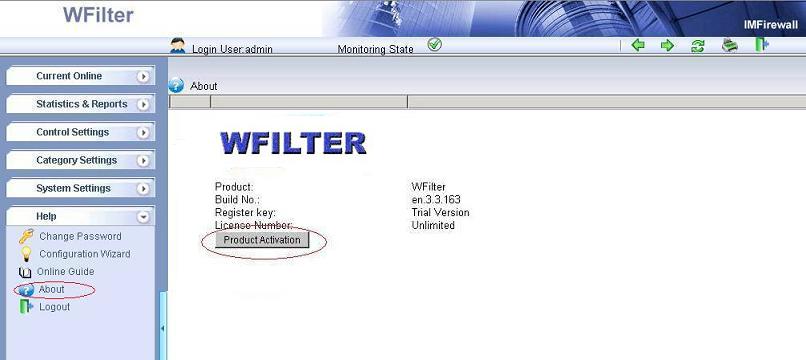
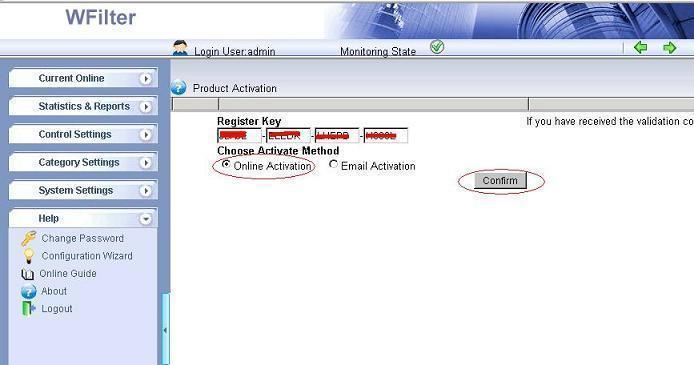
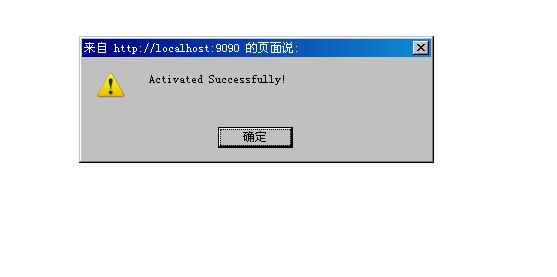
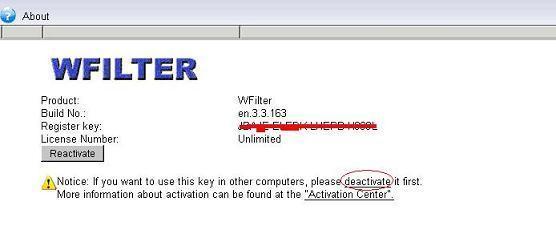
Let’s take WFilter as an example:
First, setup a mirroring port.
When the port mirroring is properly setup, WFilter will be able to monitor all computers internet activities. 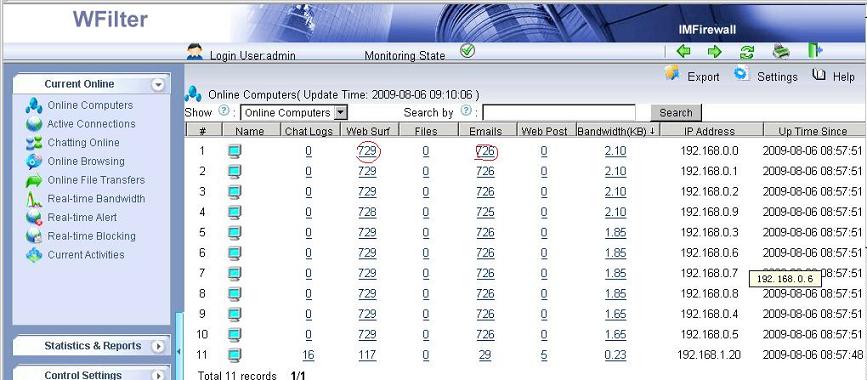
Bandwidth Management Settings
Using WFilter’s bandwidth management feature, you can set a maximum accumulating bandwidth of each computer for a period time. In this example, each user can have 200M internet bandwidth every day. Only messengers and emails are allowed when the bandwidth limit is reached.
You also can setup a policy to block certain users when available
internet bandwidth of the entire network is not enough. For example,
When entire network traffic exceeds 80% of available internet
bandwidth, p2p traffic will be blocked.
Bandwidth Alert Settings
And the bandwidth alert feature will send you an alert email when the accumulating bandwidth of a computer is too large.
More information, please check “WFilter Enterprise”.
Other related links:
How to block websites at work during working hours?
How to block video streaming on company network?
How to block internet downloading?
How to monitor internet bandwidth?
How to monitor internet usage on company network?
How to block instant messaging on company network?
How to filter websites and restrict website access?