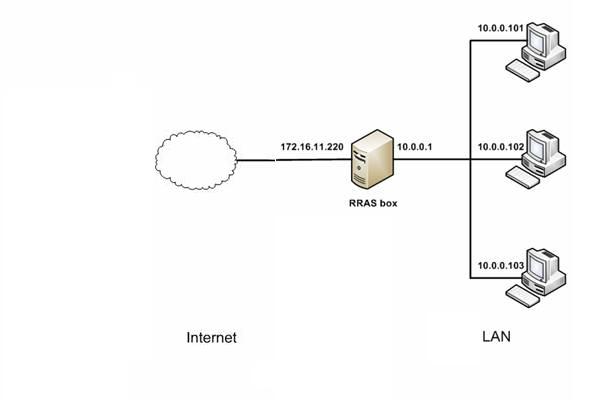
PPPOE is widely used for user authentication and traffic accounting. However, it’s a little difficult to monitor and filter PPPOE clients’ internet usage and behavior.
In this example, we will demonstrate you to monitor and filter PPPOE clients with WFilter Free. Please notice that only non-encrypted and uncompressed PPPOE traffic can be supported. So the first step is to configure your PPPOE server for non-encryption and non-compression.
1. PPPOE server settings
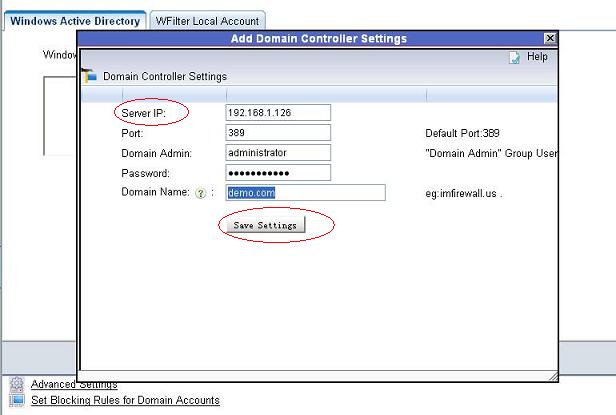
Let’s take windows 2003 and RouteOS for examples.
1). 2003 Server Configuration
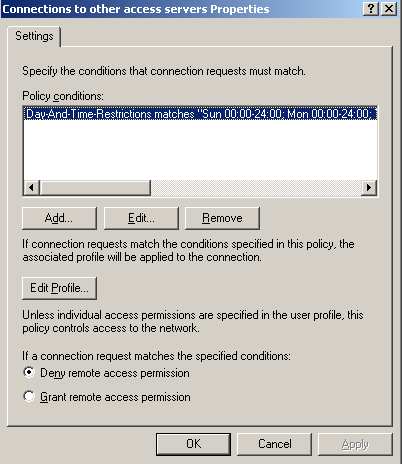
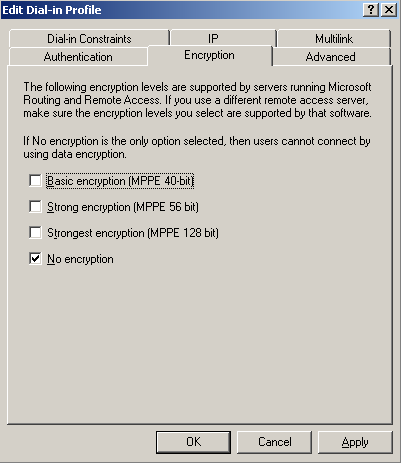
If you are using windows 2003 server as the PPPOE server, please follow below steps to configure:
In “Properties” of the “Routing and Remote Access”, disable “software compression” and “LCP” in the “PPP” tab.

Edit “remote access policy” for “no encryption” in “Edit Profile”. Notice: The default two policies shall all be modified.
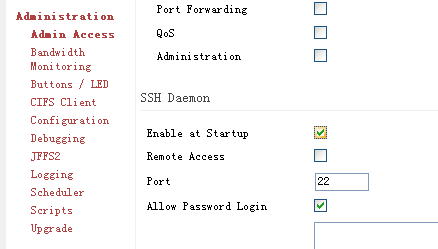
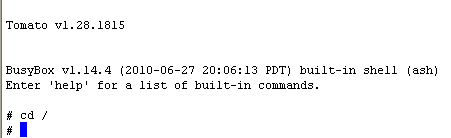
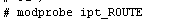
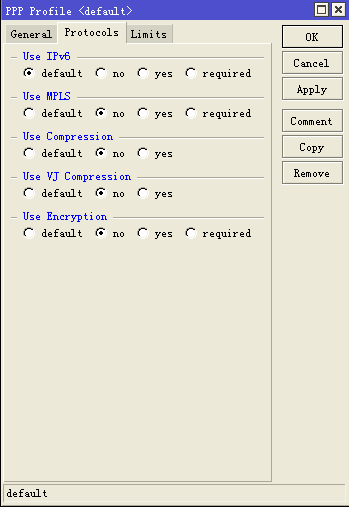
2). ROS Configuration
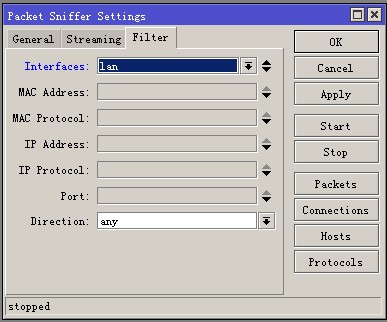
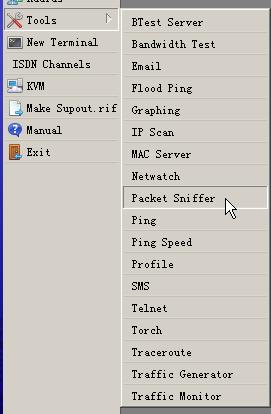
If you are using routeOS as PPPOE server, please follow these steps to disable compression and encryption:
In “PPP” tab of “Profiles”, click “Protocols” and disable compression and encryption.
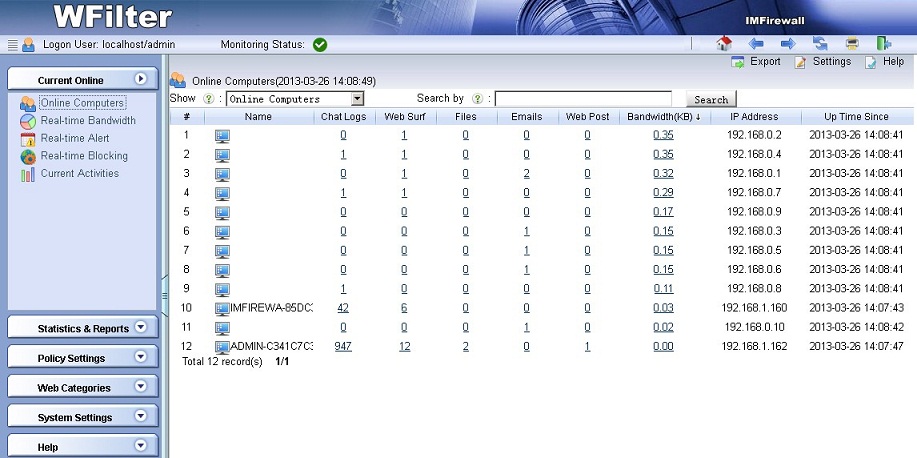
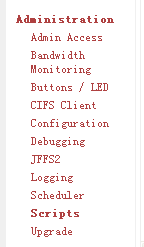
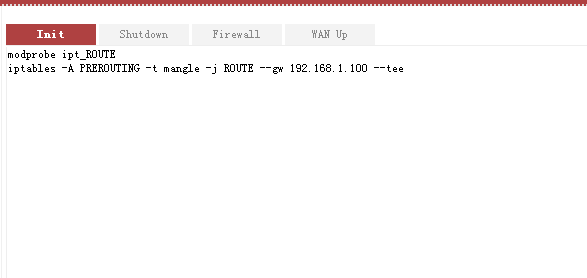
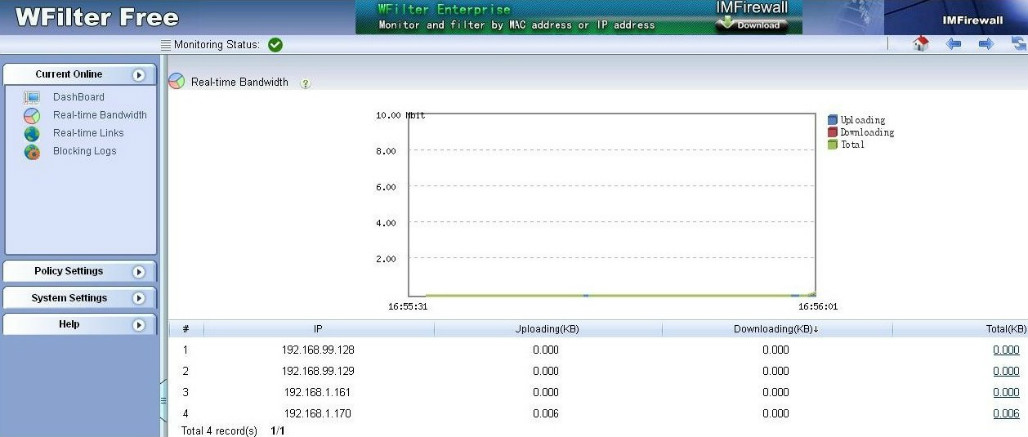
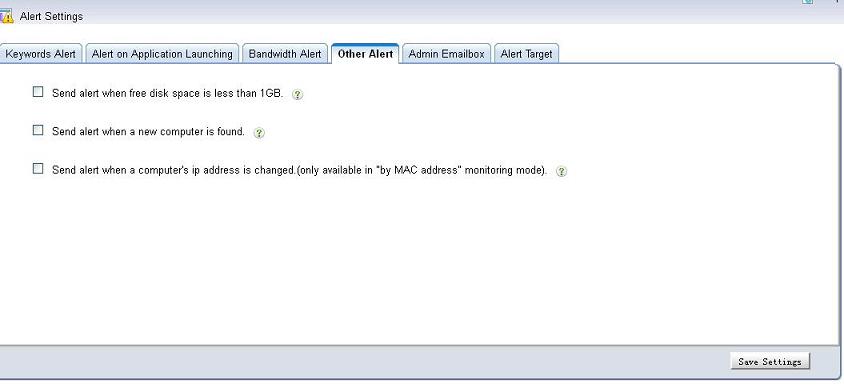
2. Monitor PPPOE clients in WFilter
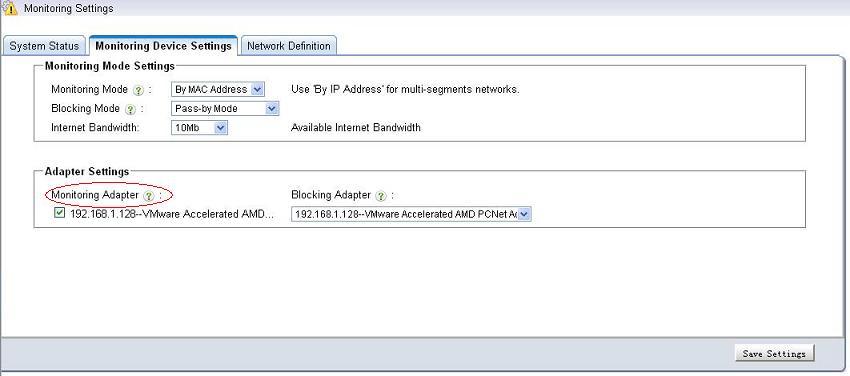
2.1) Choose the internal adapter
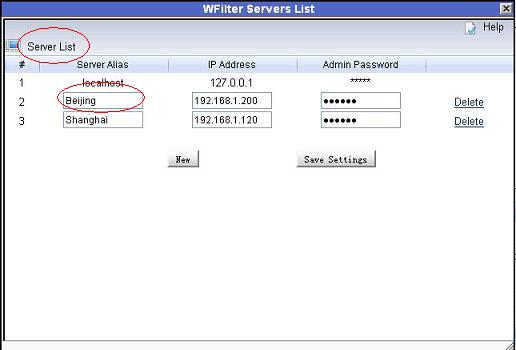
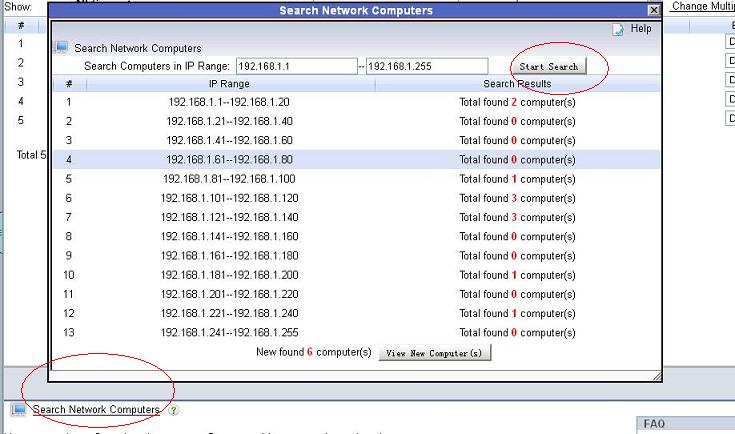
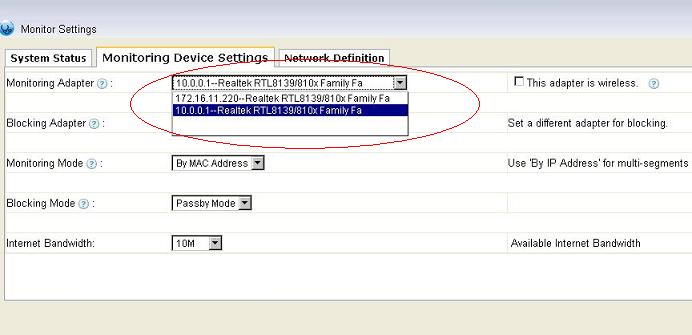
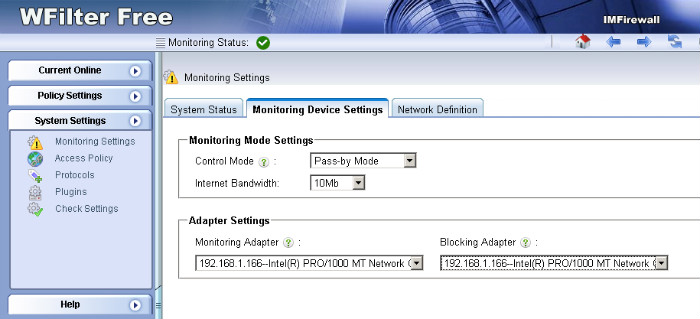
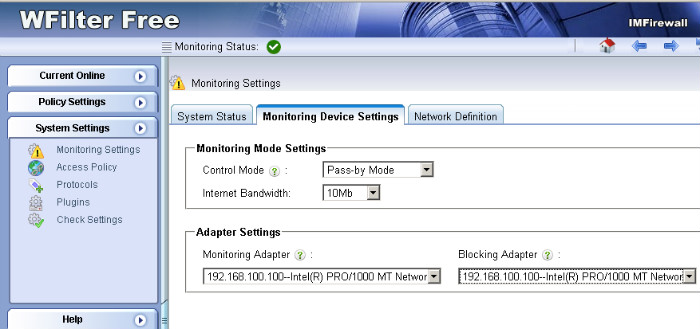
Now WFilter is able to parse PPPOE traffic. In this example, we just install WFilter free in the windows 2003 PPPOE server.
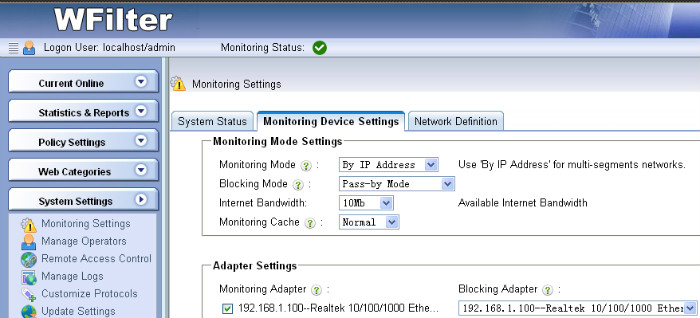
You need to choose the internal adapter as the “monitoring adapter” in “System Settings”->”Monitoring Settings” of WFilter.
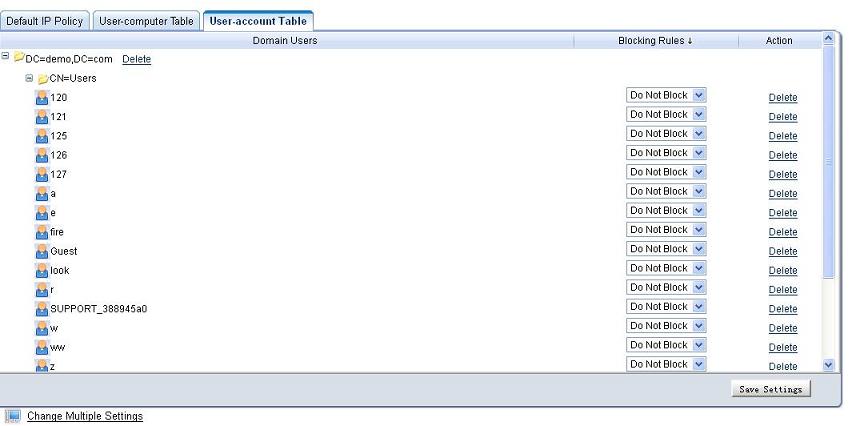
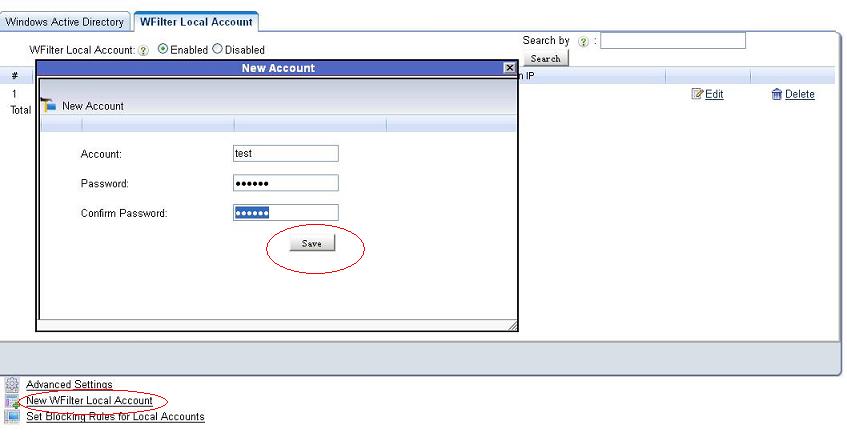
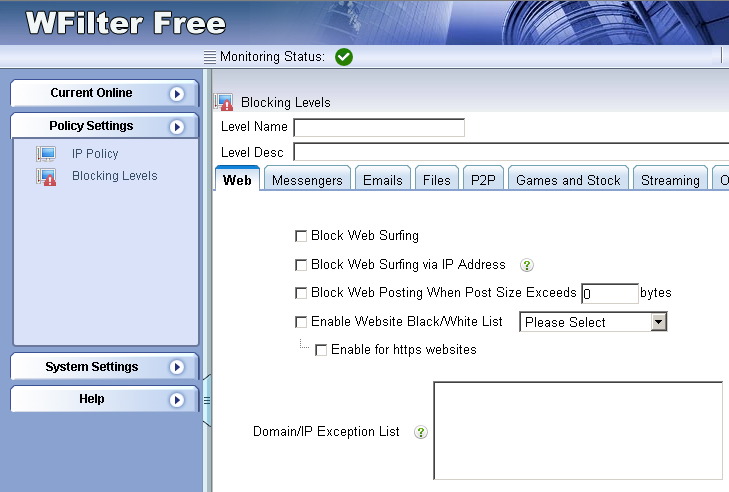
2.2). Setup client policy
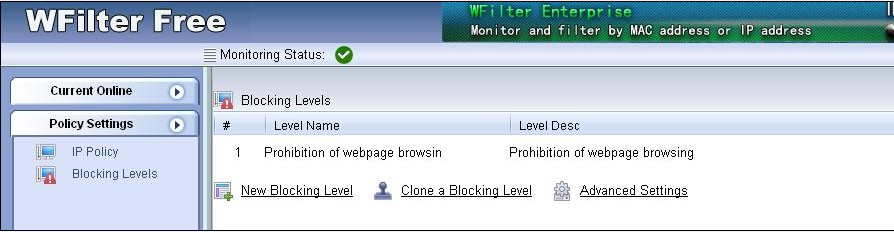
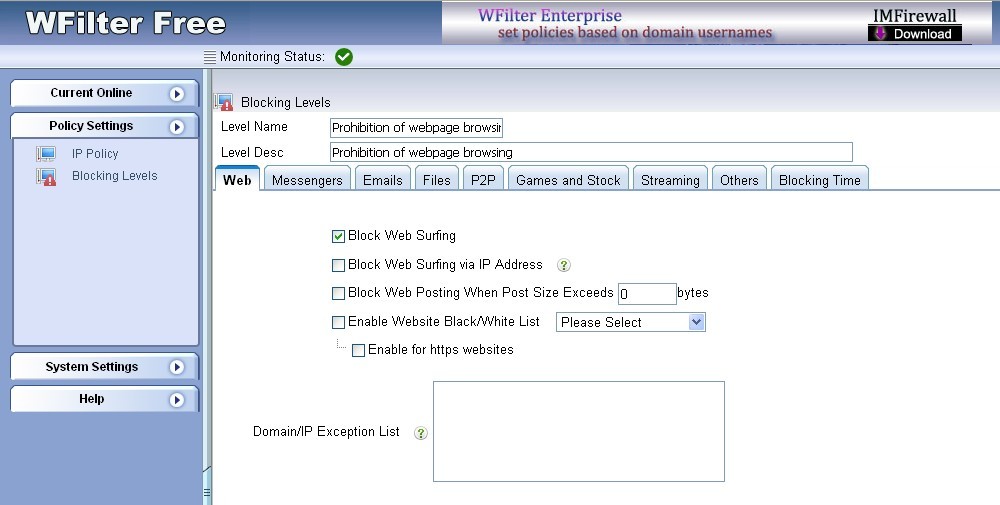
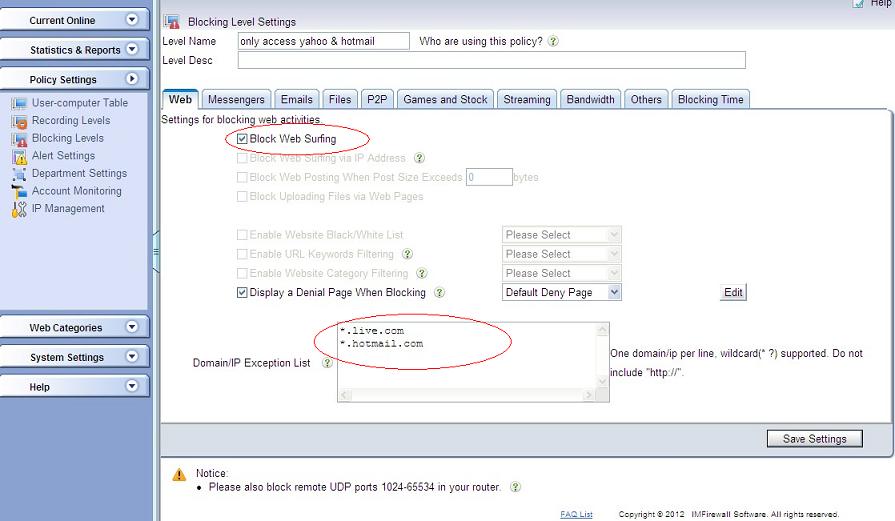
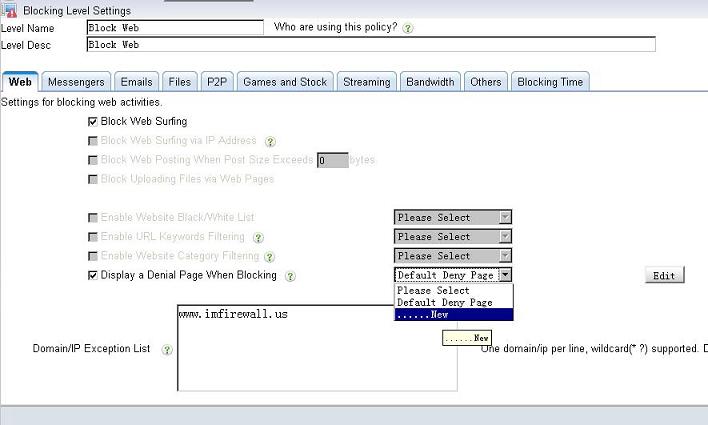
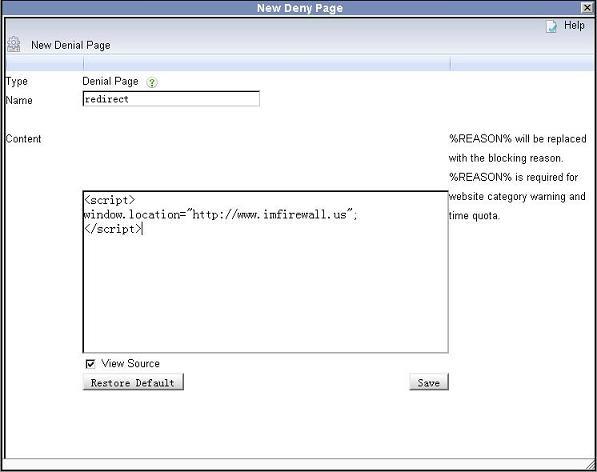
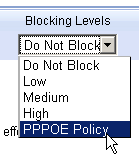
Add a block policy to block web surfing.
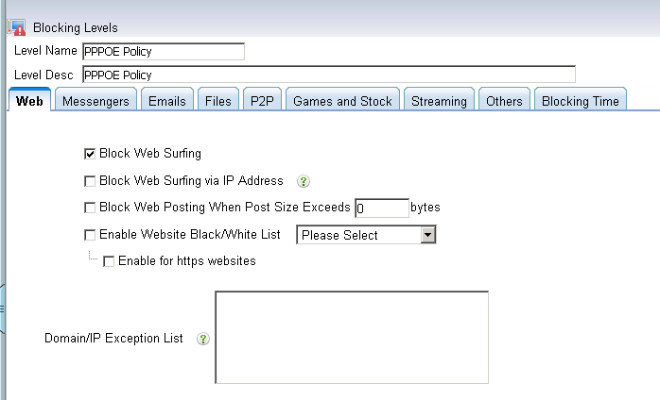
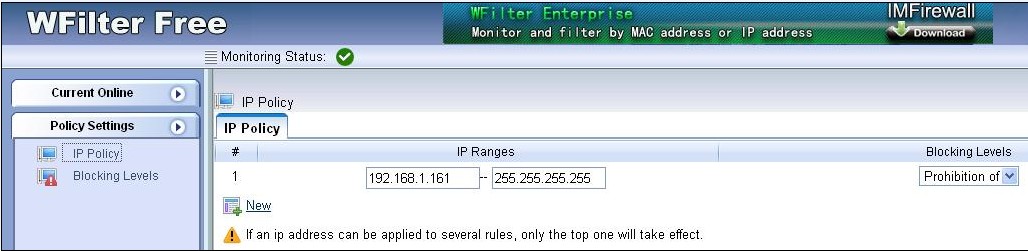
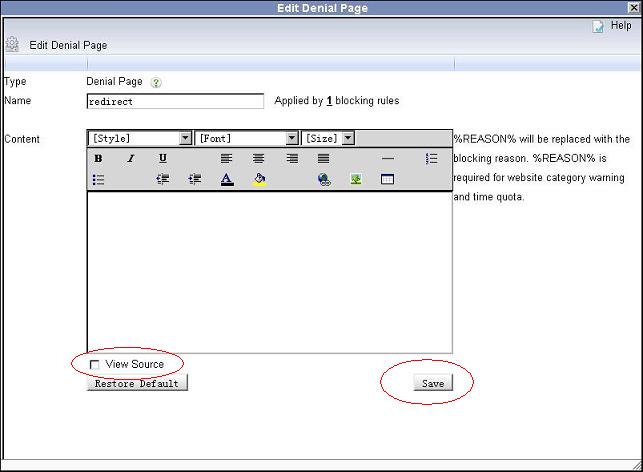
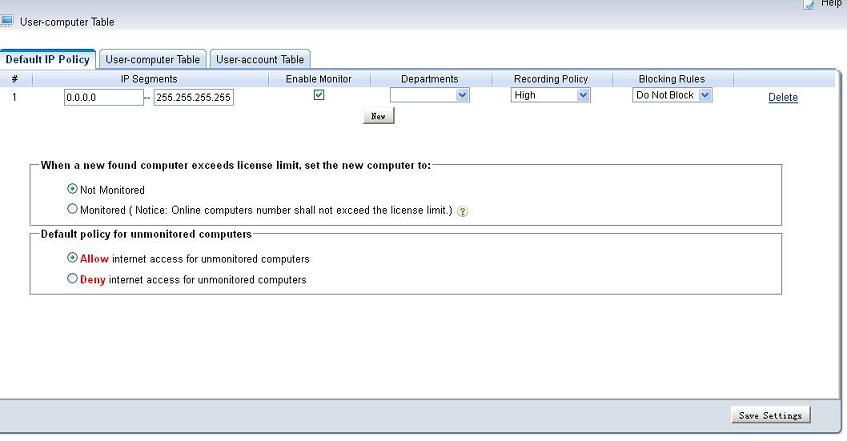
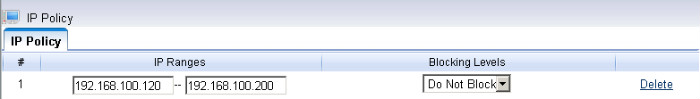
Apply this policy to PPPOE clients’ ip ranges
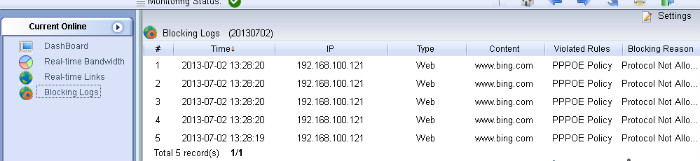
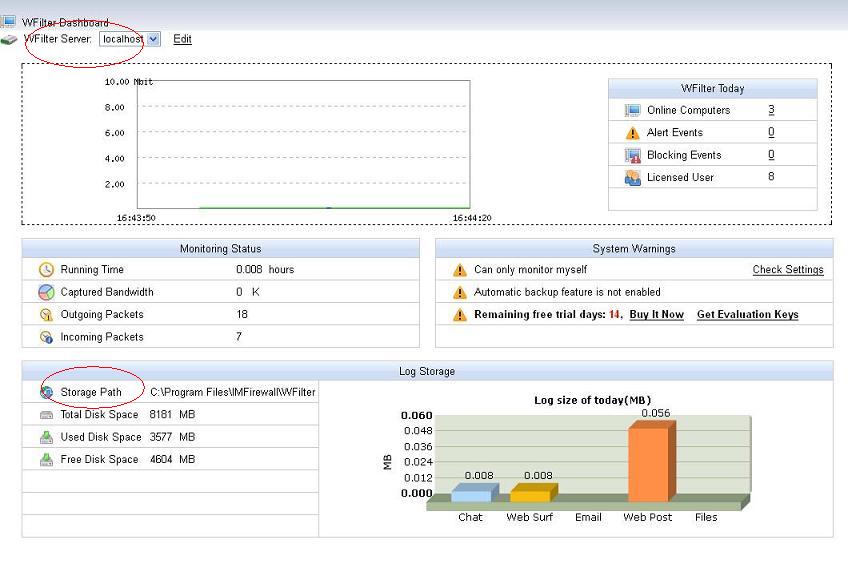
2.3). Check Blocking
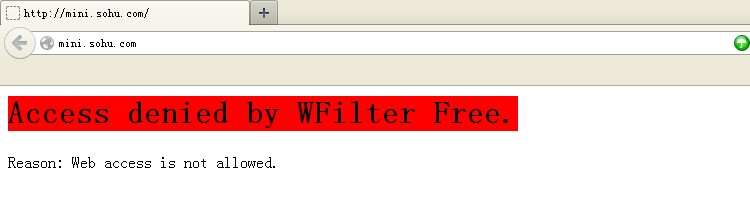
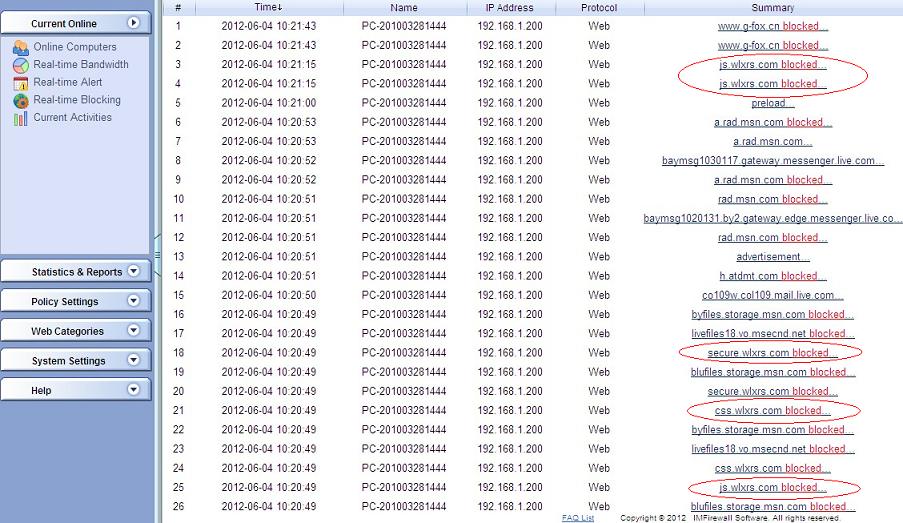
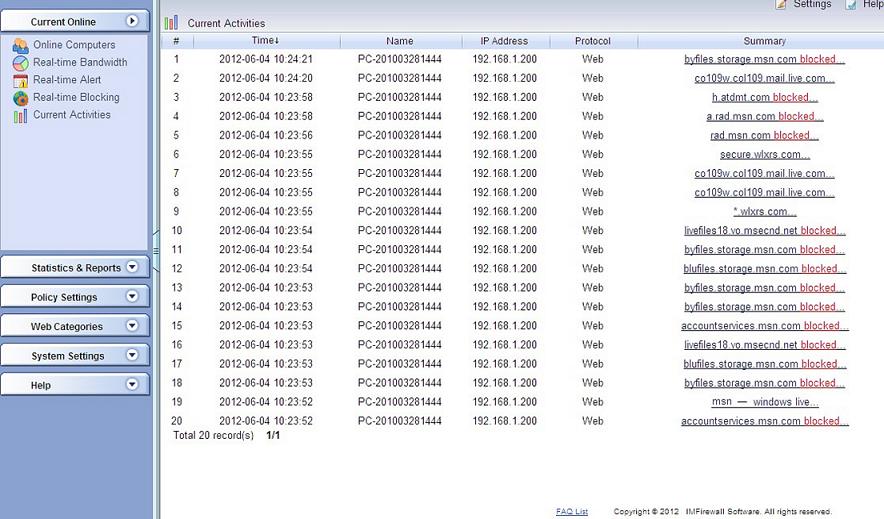
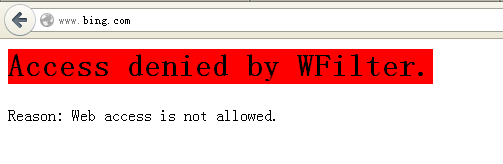
PPPOE clients get blocked.
Blocking events in WFilter.