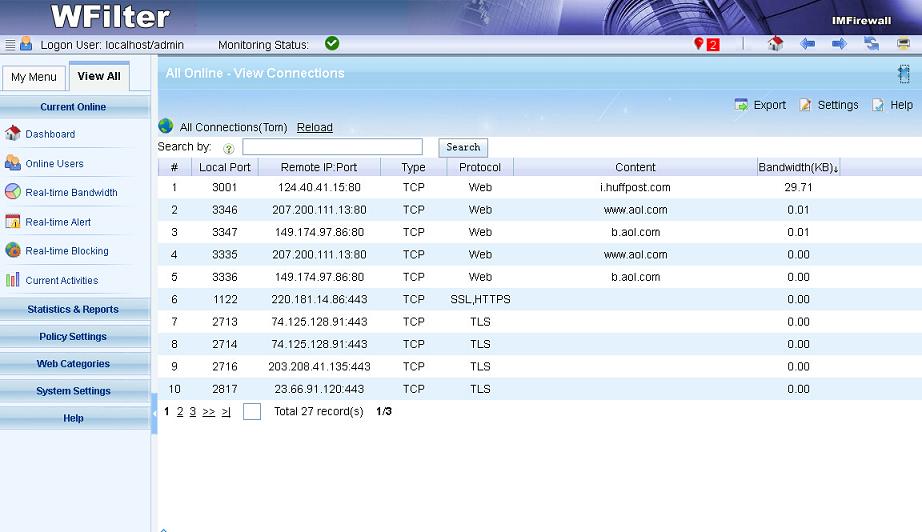
Torrent downloading is annoying and can consume most of your bandwidth, so you might want to block torrent in your network. There are several ways to block torrent in your network. While in this post, I will introduce three solutions to block torrent(bittorrent, utorrent, qtorrent) with WFilter internet content filter and WFilter NG firewall.
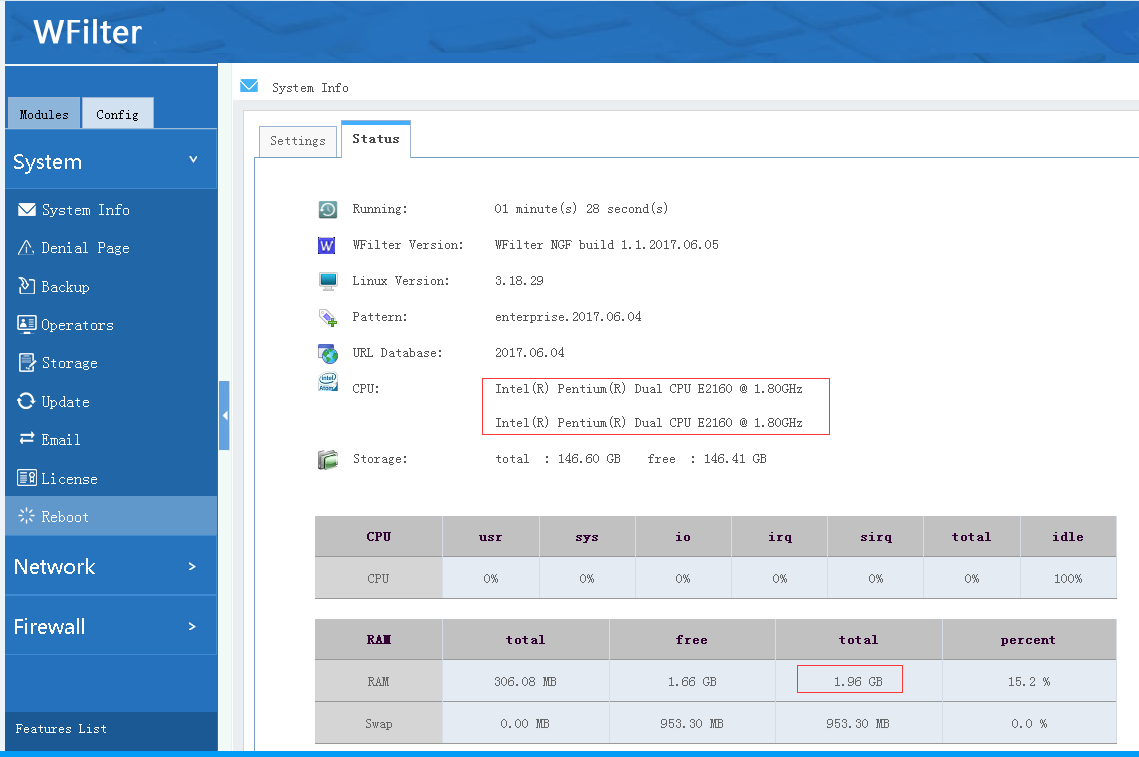
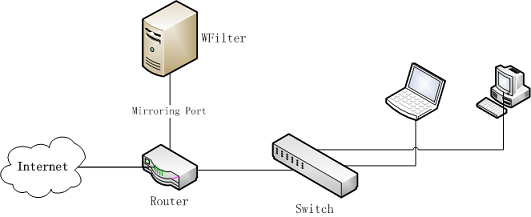
Please be aware that “WFilter internet content filter(ICF)” and “WFilter NG firewall(NGF)” are total different products. WFilter ICF is a windows program, which is designed for pass-by deployment on a mirroring port. While WFilter NGF is a dedicated linux firewall system.
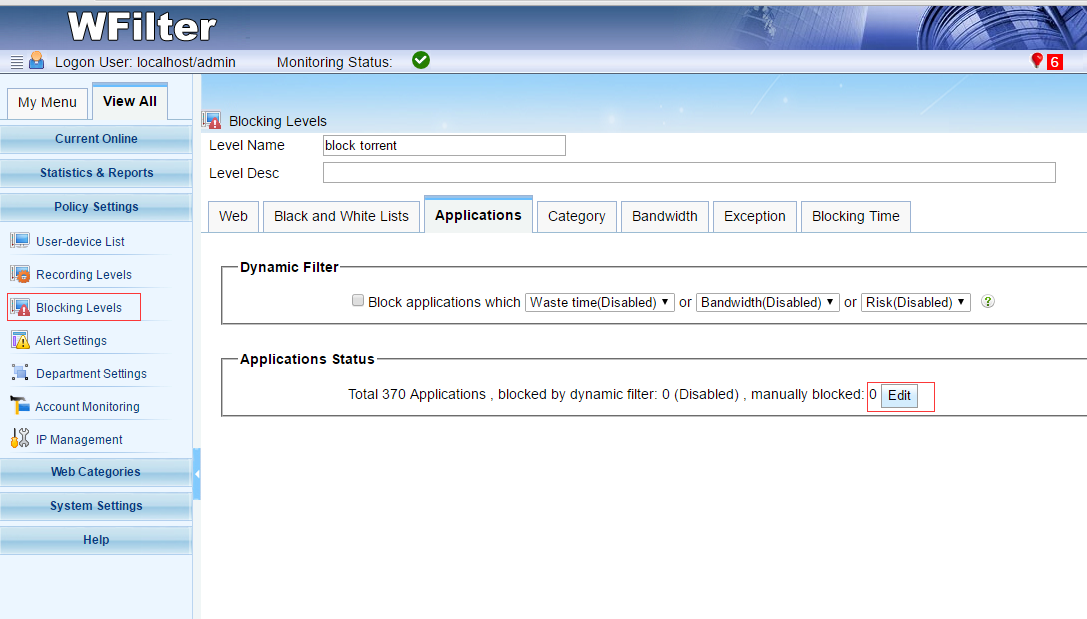
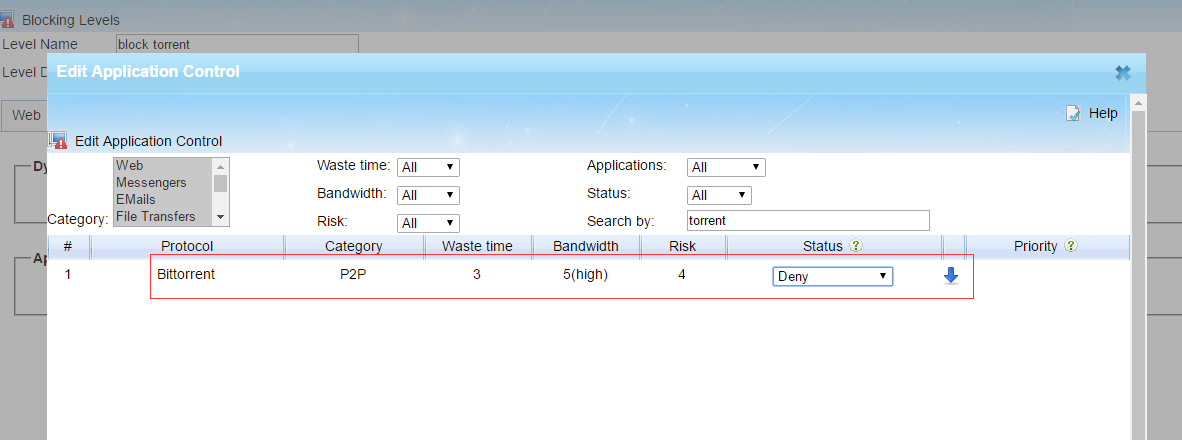
1. Block torrent with WFilter ICF
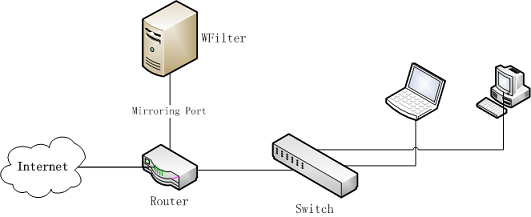
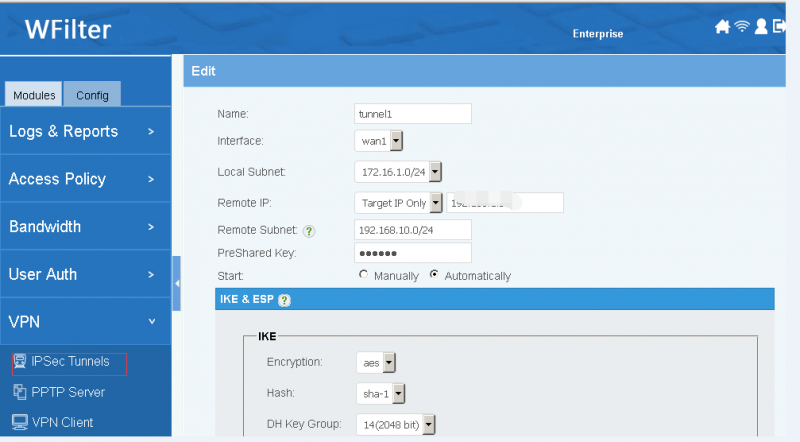
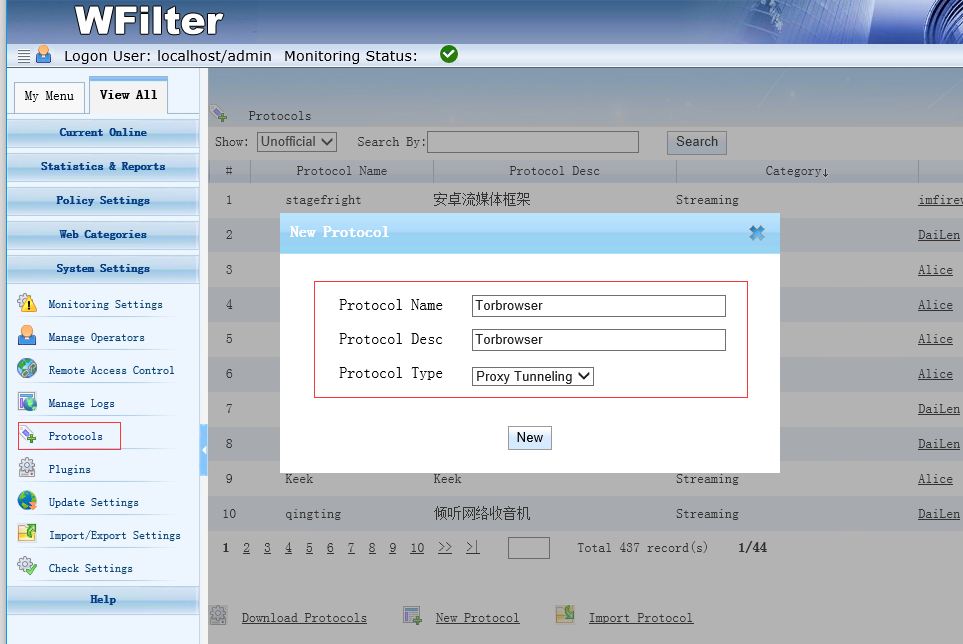
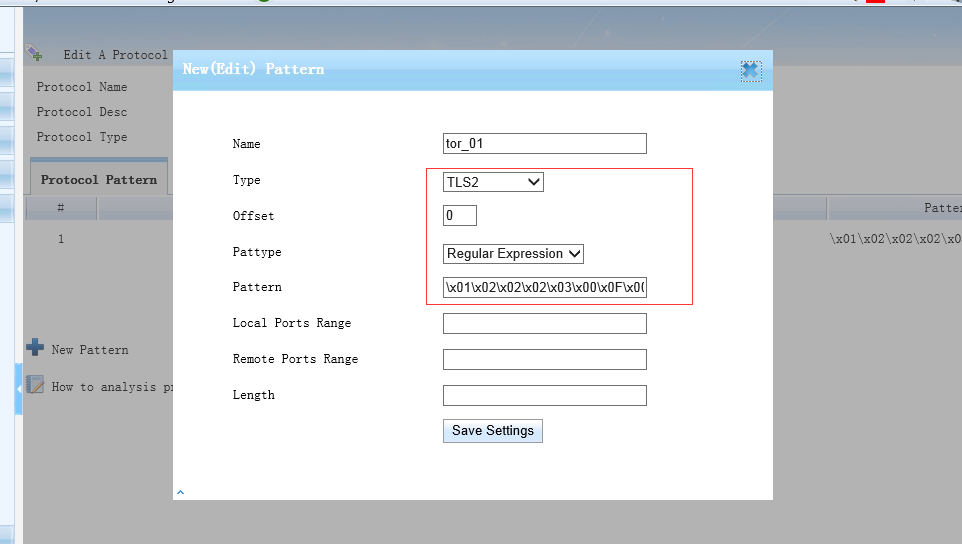
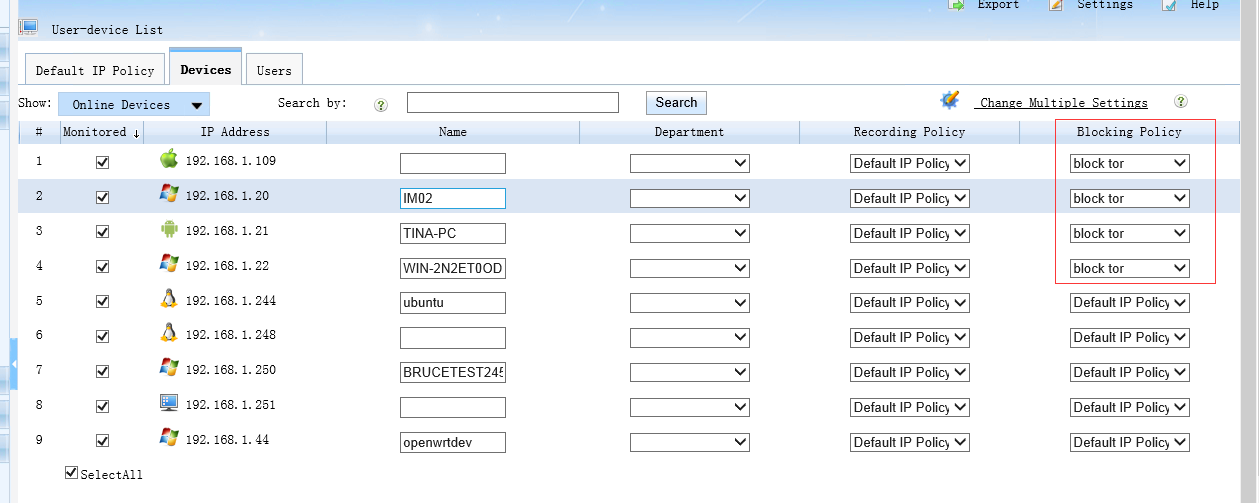
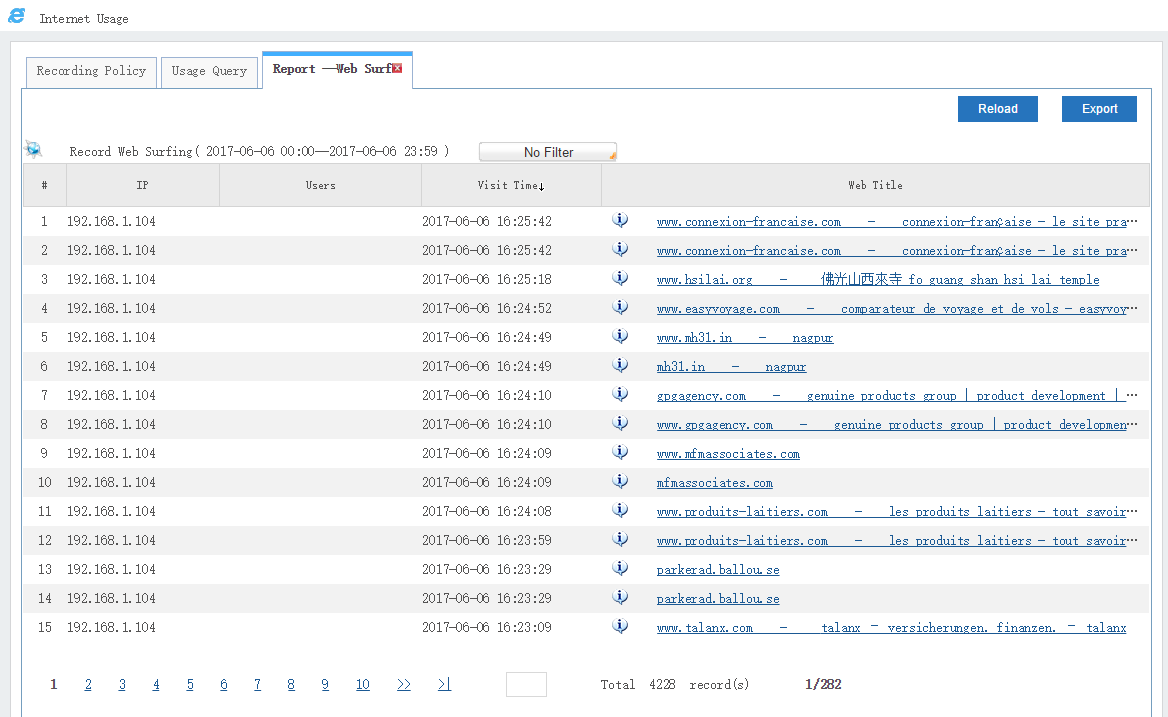
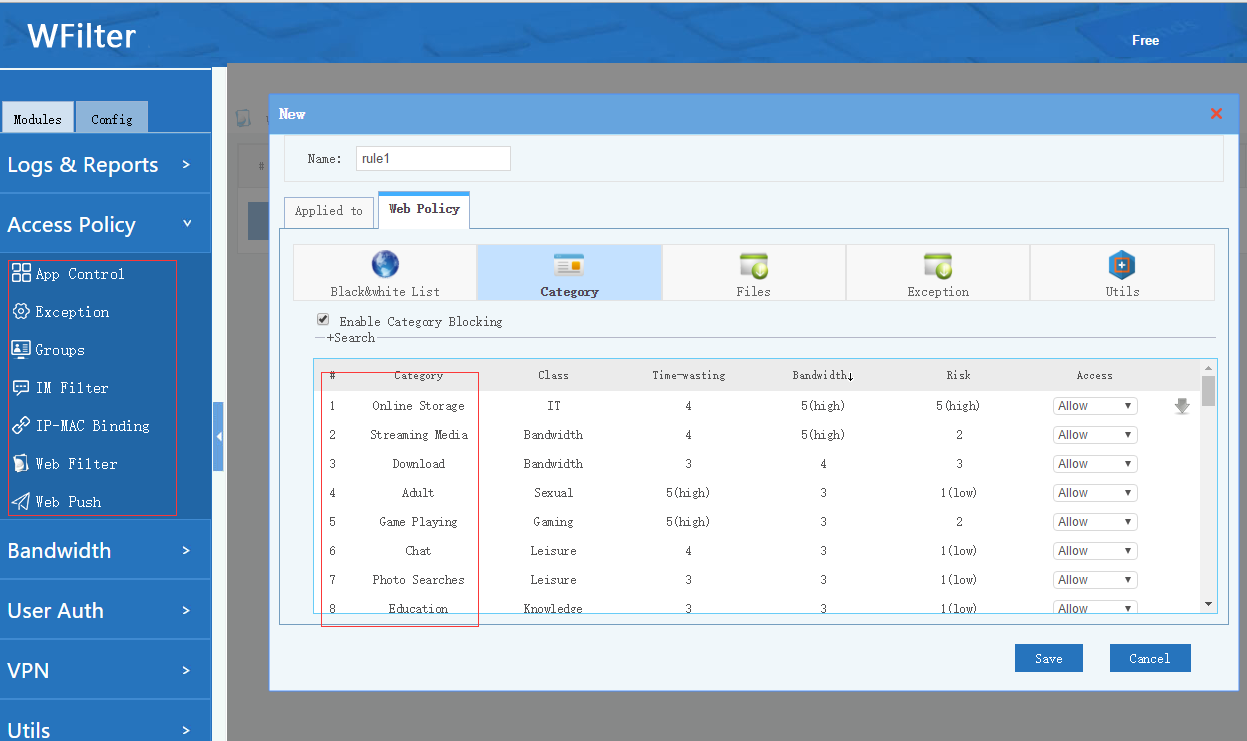
As you can see in the diagram, the WFilter internet content filter(ICF) shall be connected to a mirroring port in your router or switch. So it can analysis network packets and deploy internet access policies. Steps to block torrent with WFilter ICF:
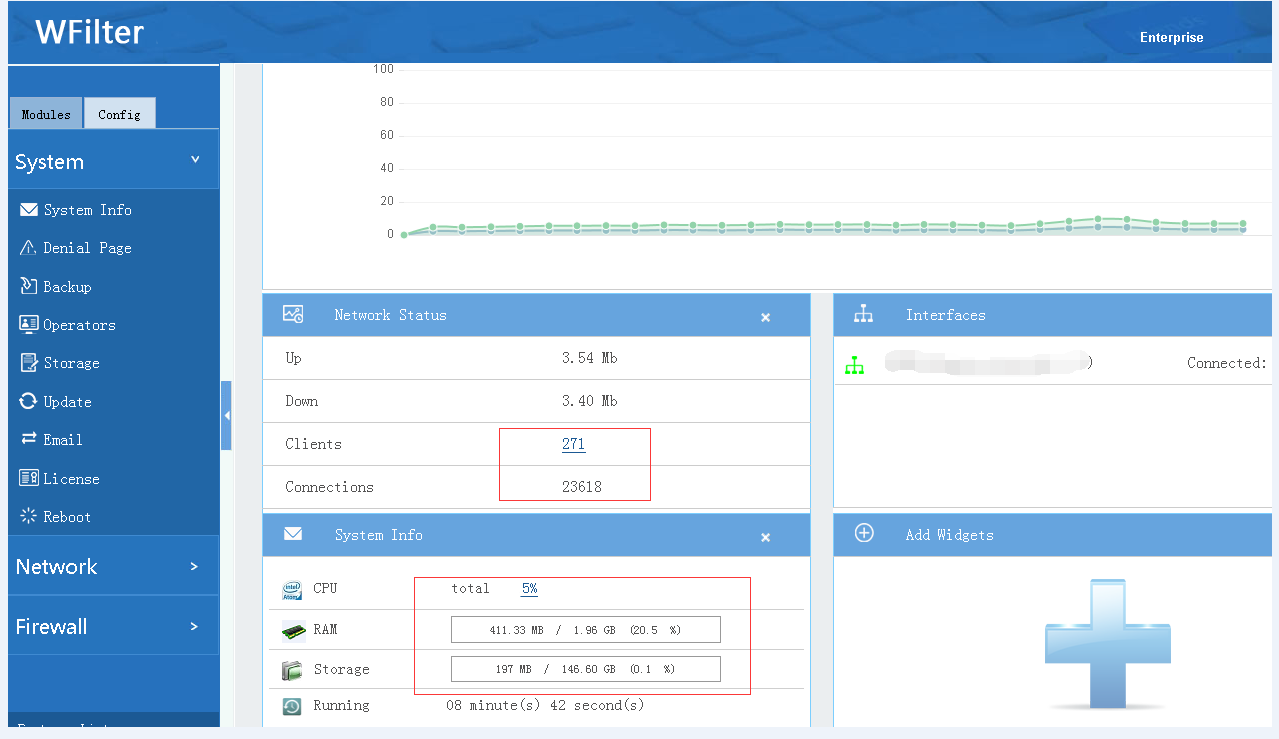
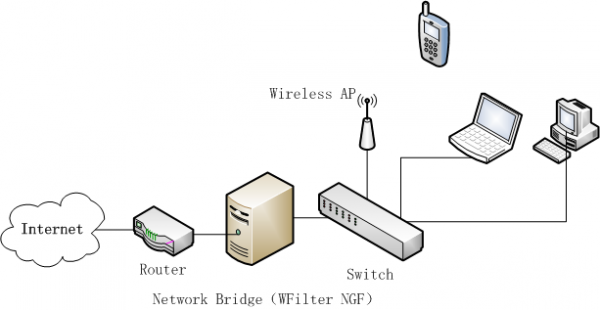
2. Block torrent with WFilter NGF as a network bridge.
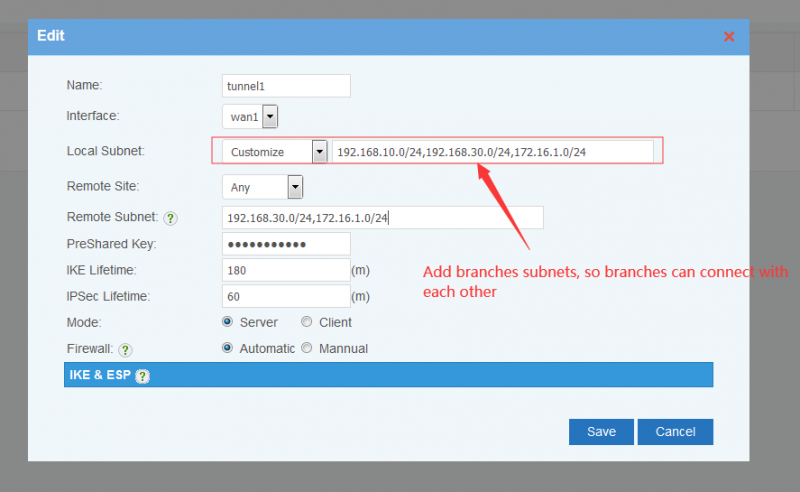
Network topology diagram:
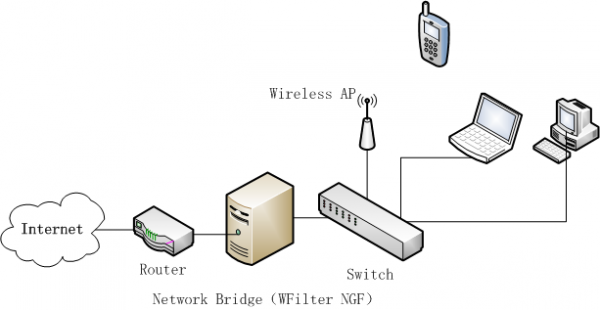
WFilter NGF acts as a network bridge, sitting between your router and switch. So it can filter internet traffic.
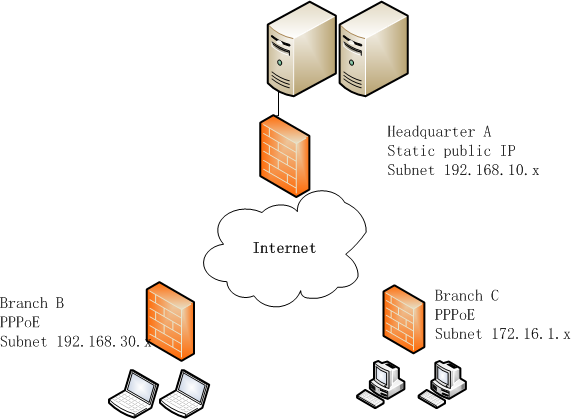
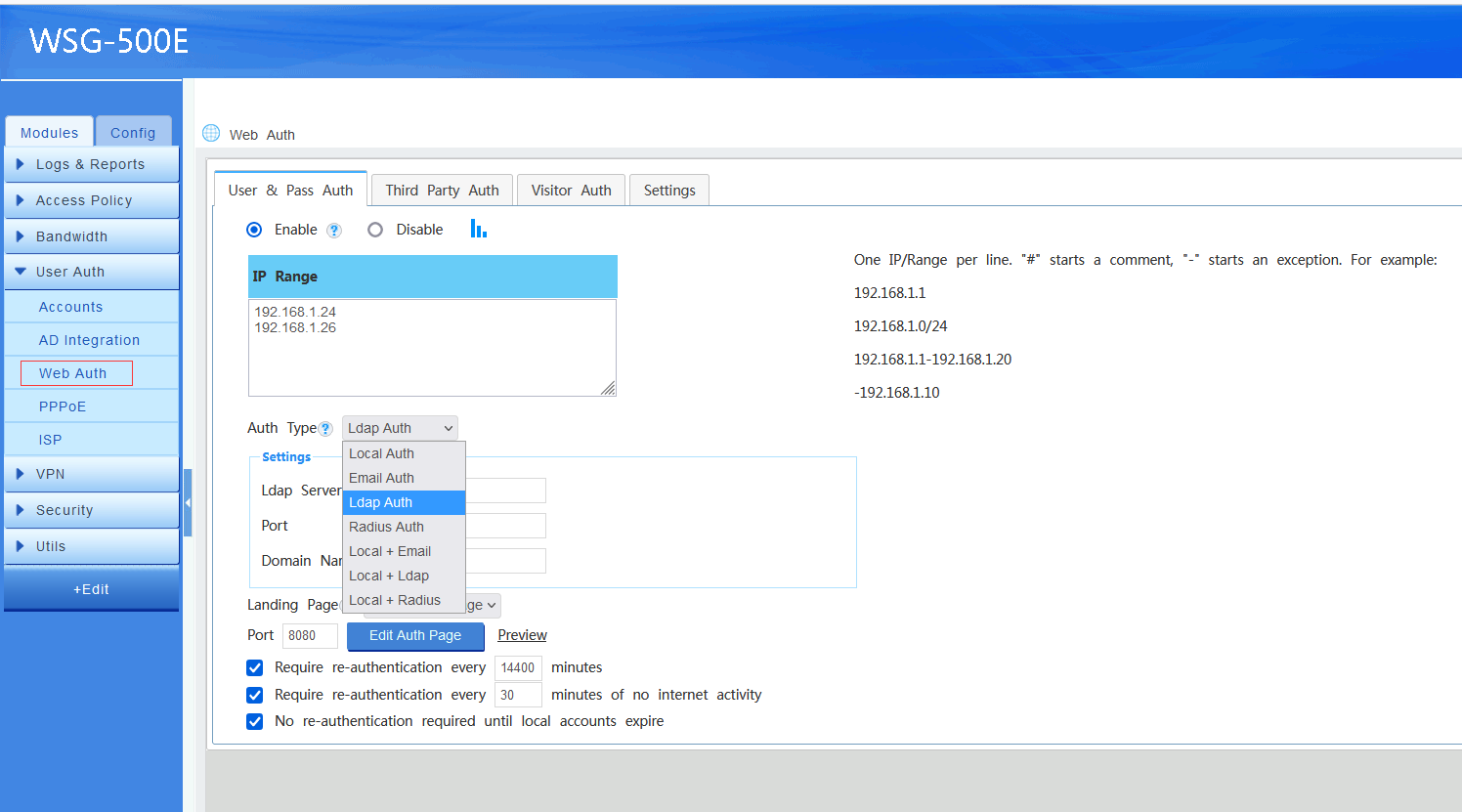
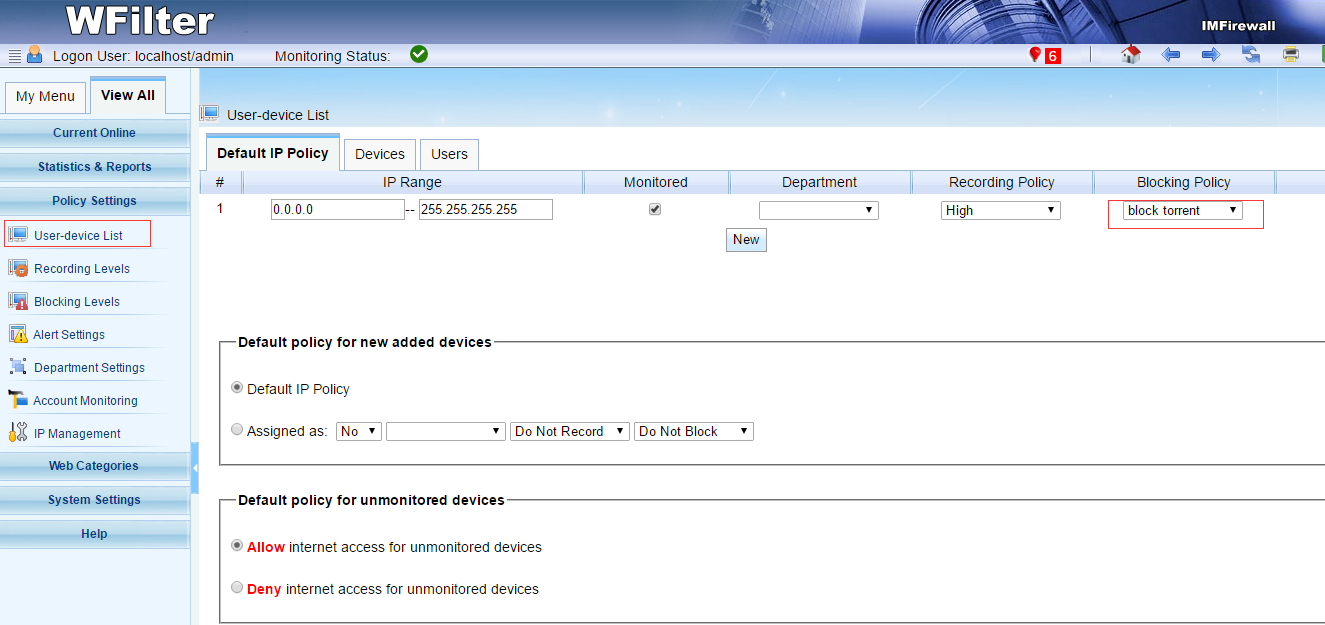
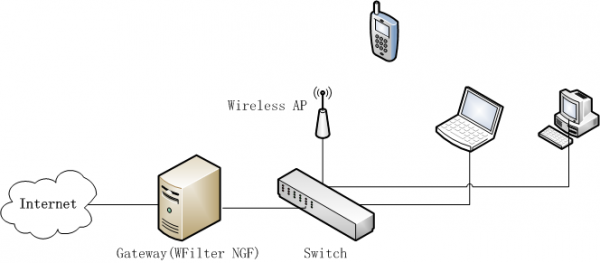
3. Block torrent with WFilter NGF as a network gateway.
Network topology diagram:
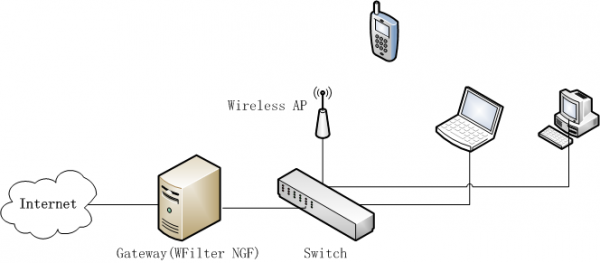
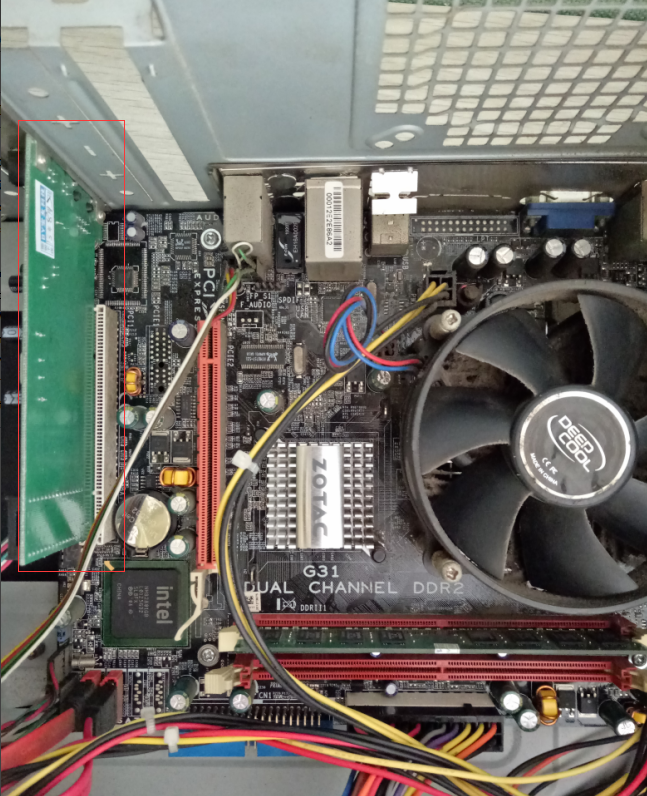
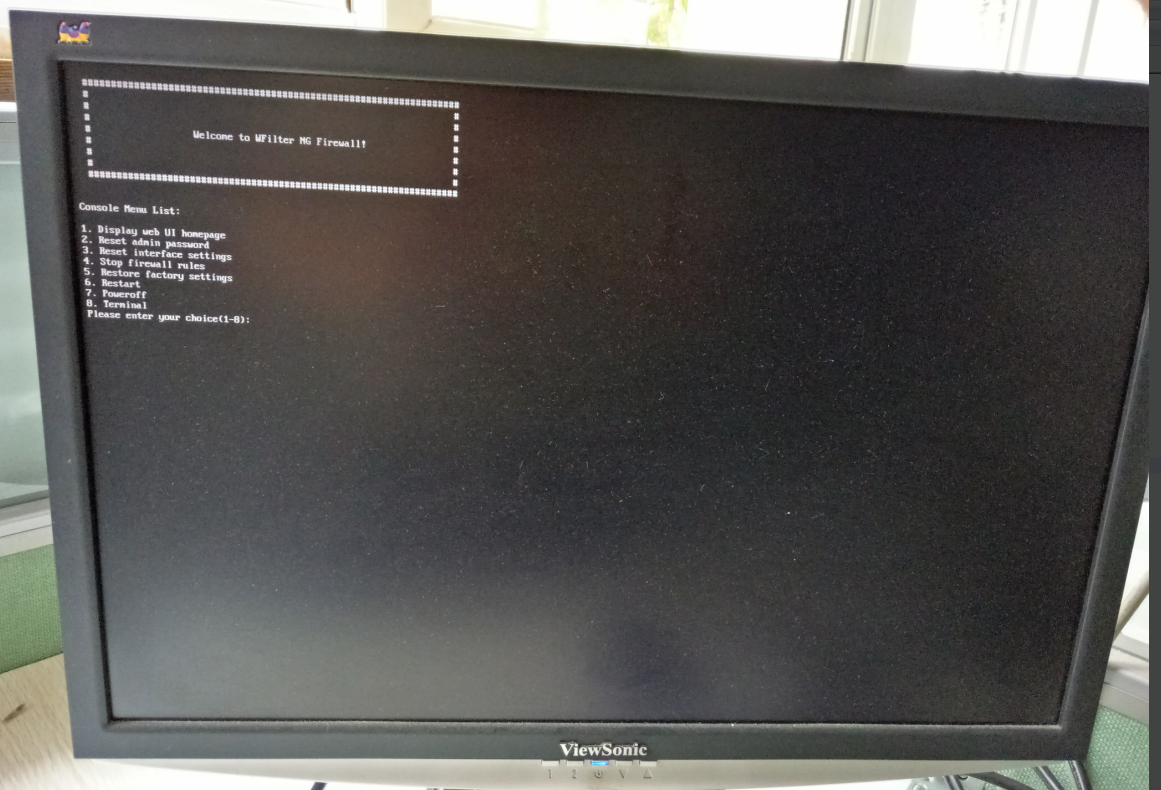
In this topology, WFilter NGF acts as the gateway of your network to deploy internet access policies. Please be aware that you can install WFilter NGF in a virtual machine to act as a virtual gateway, here is a guide: Using a pre-built VMWare image of WFilter NG Firewall
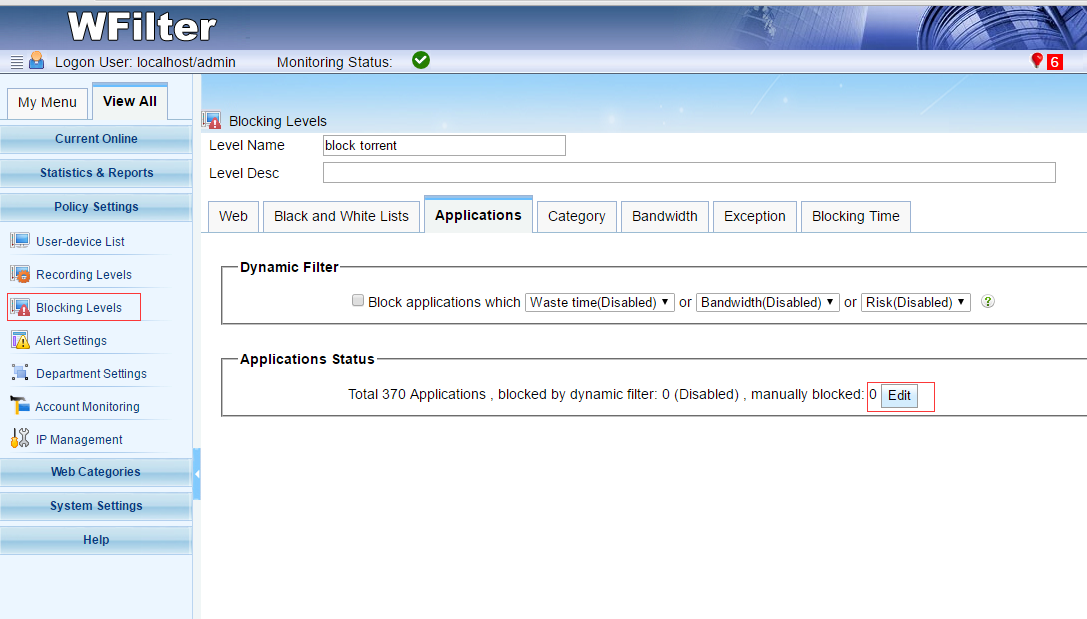
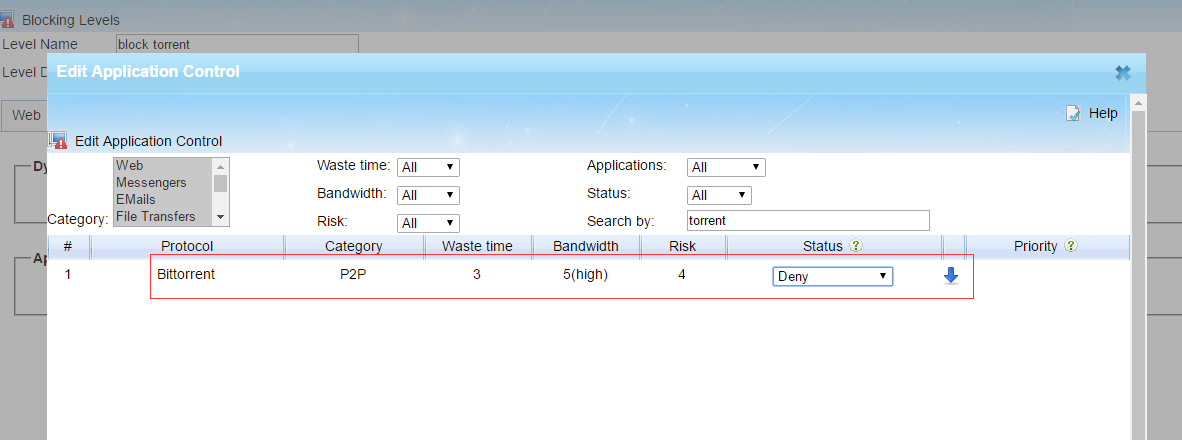
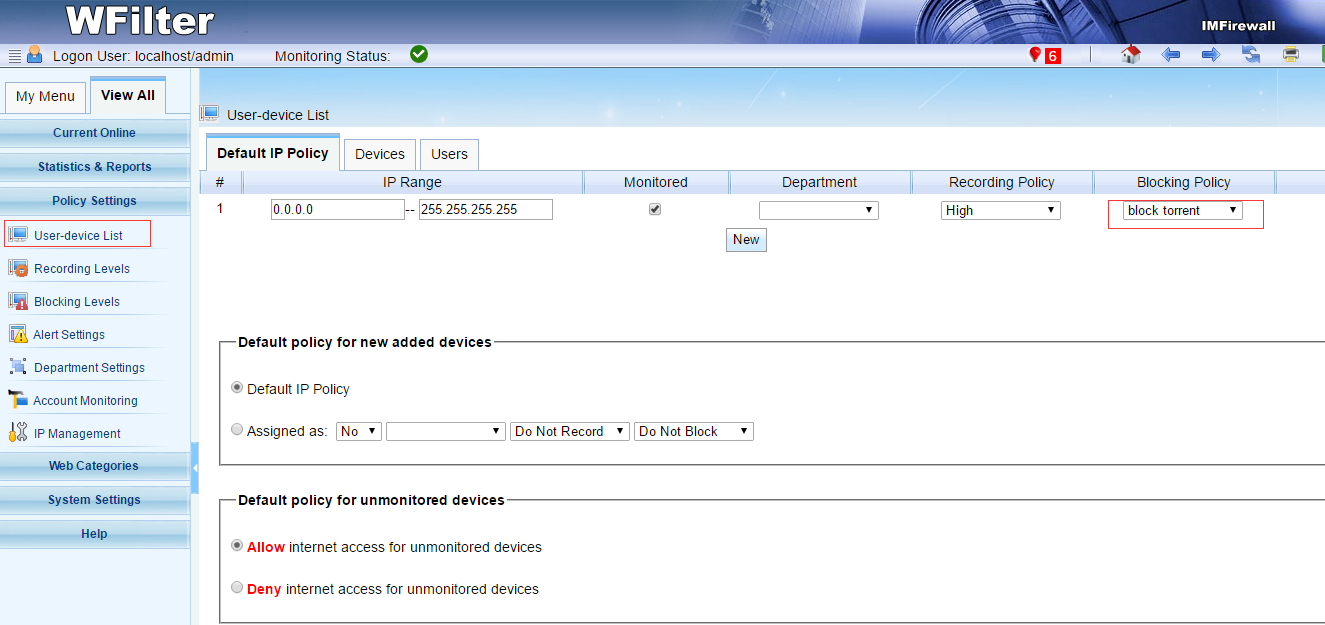
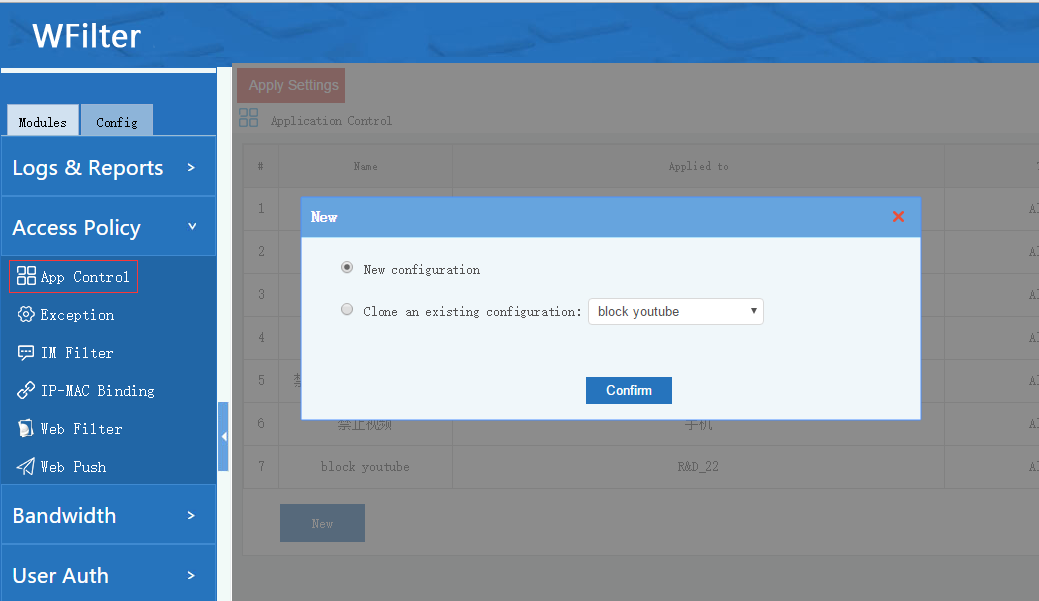
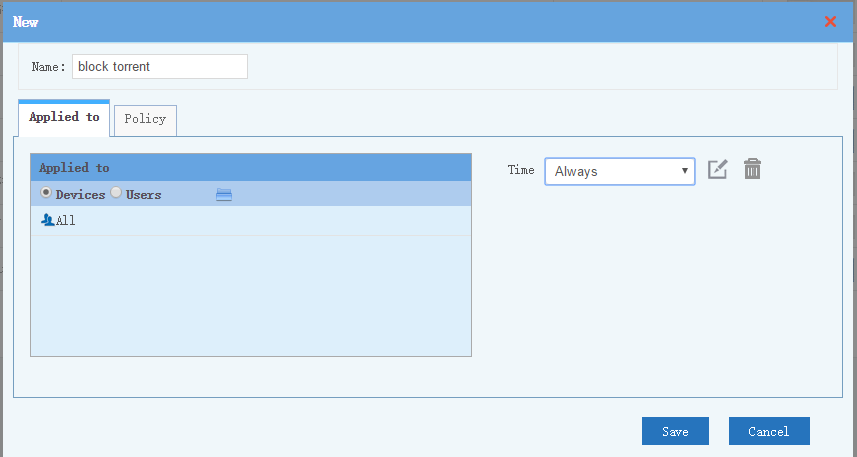
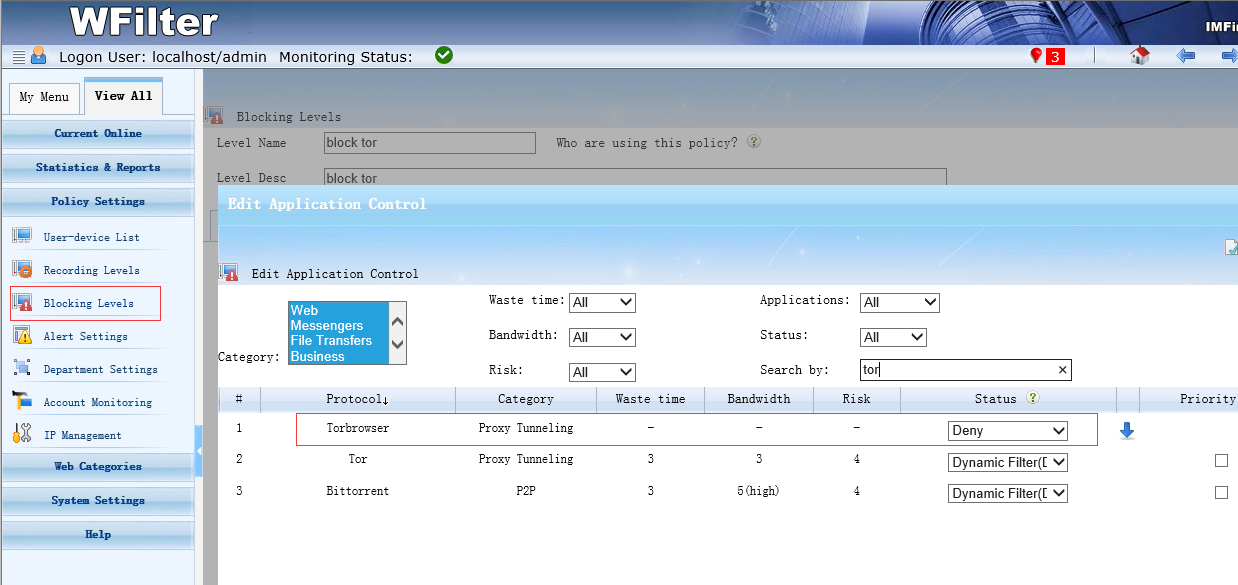
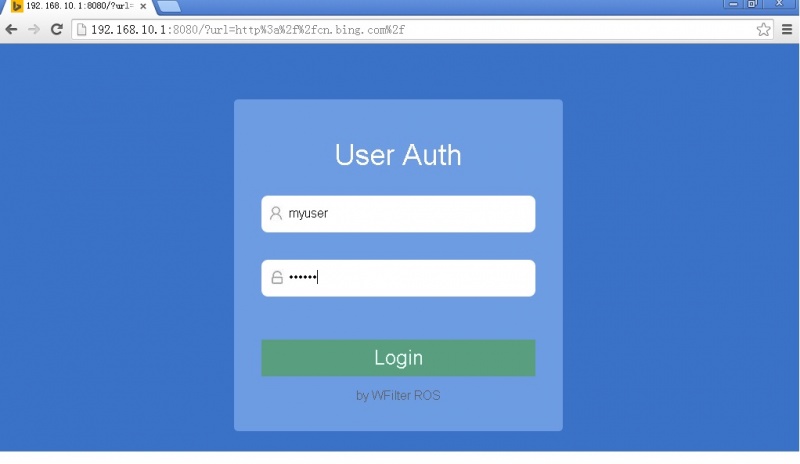
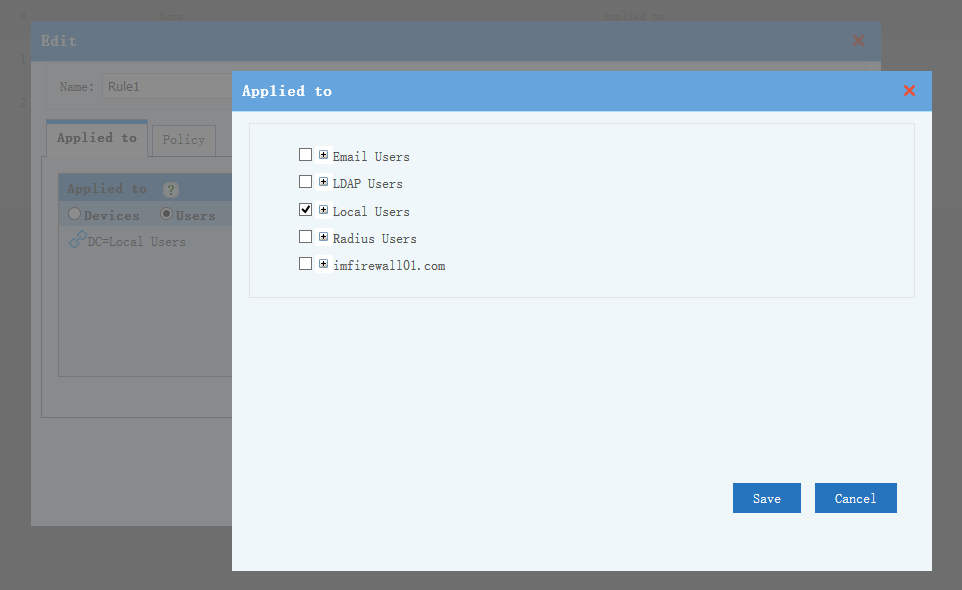
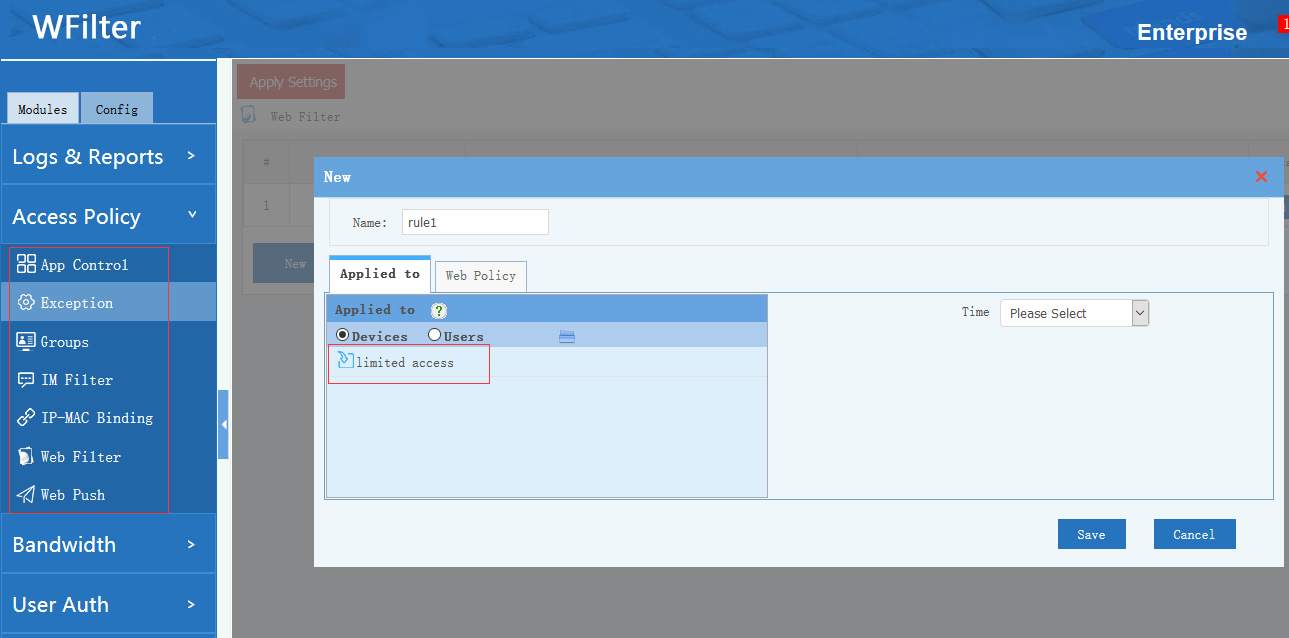
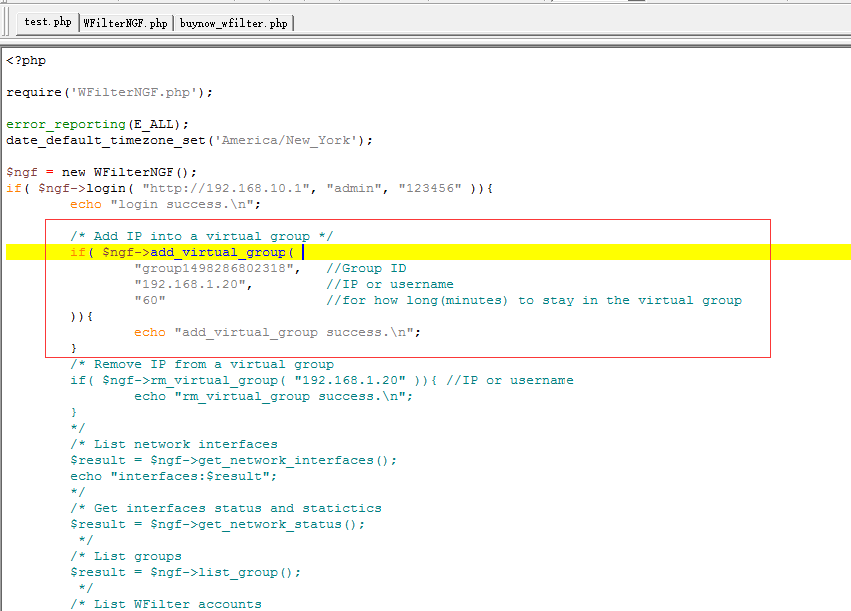
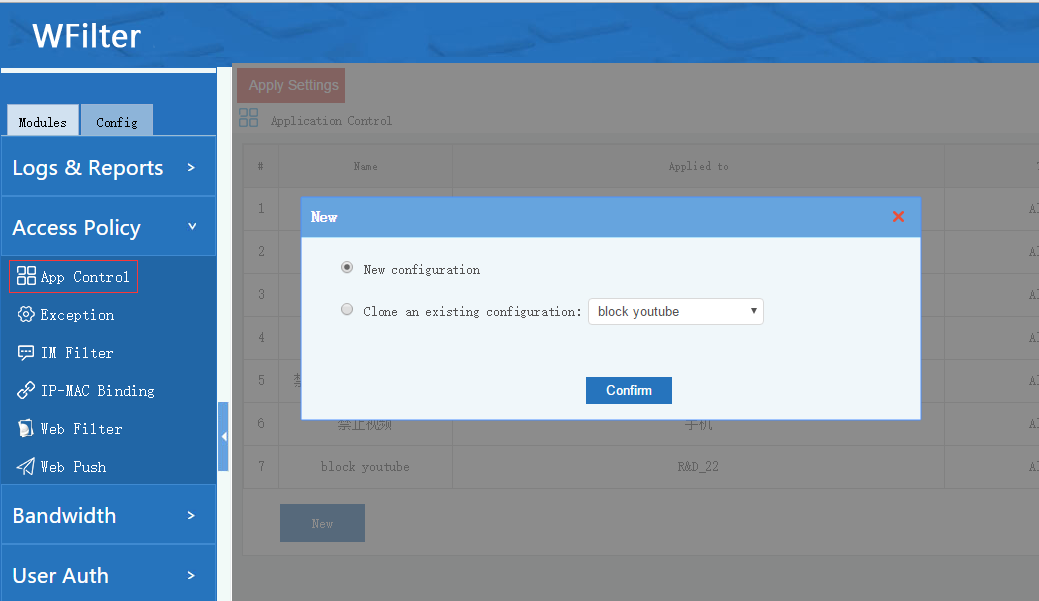
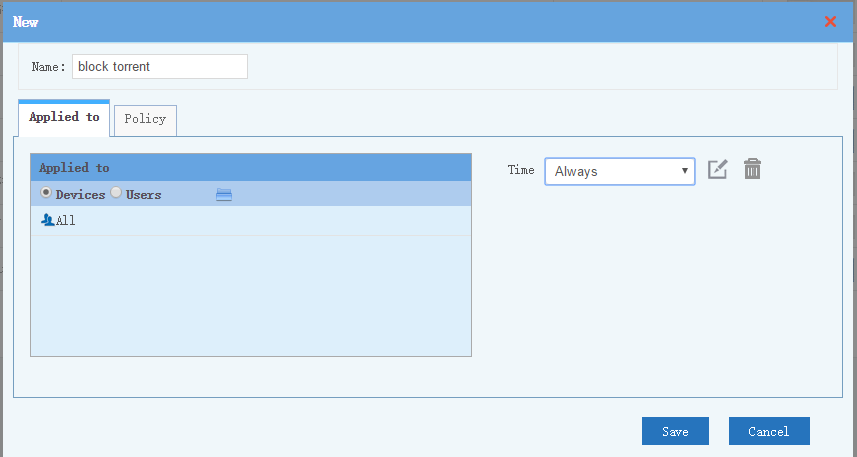
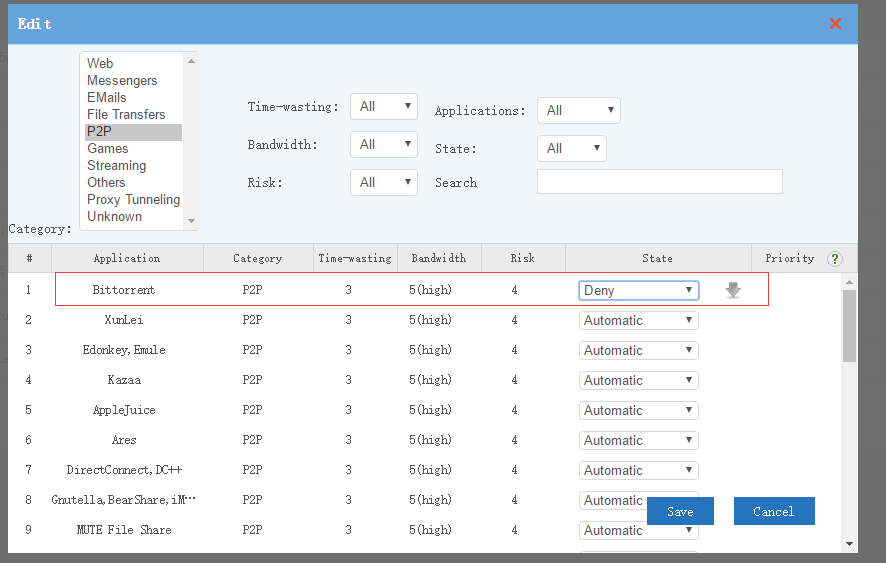
You can setup “application control” policies to block torrent with below steps:
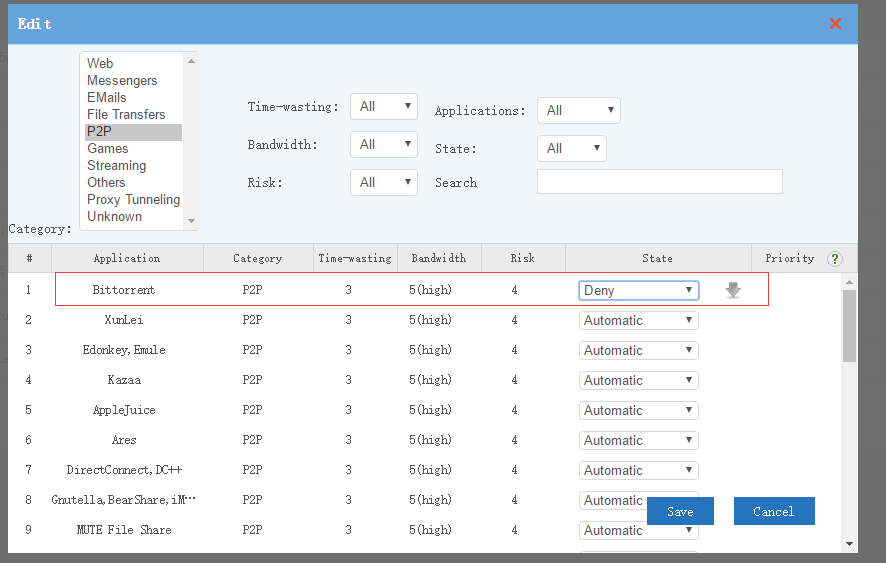
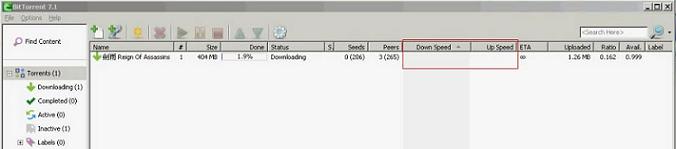
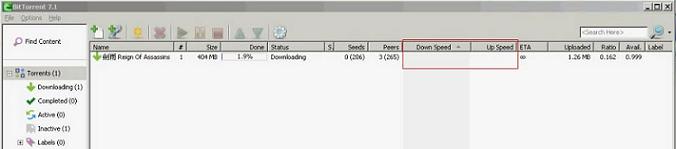
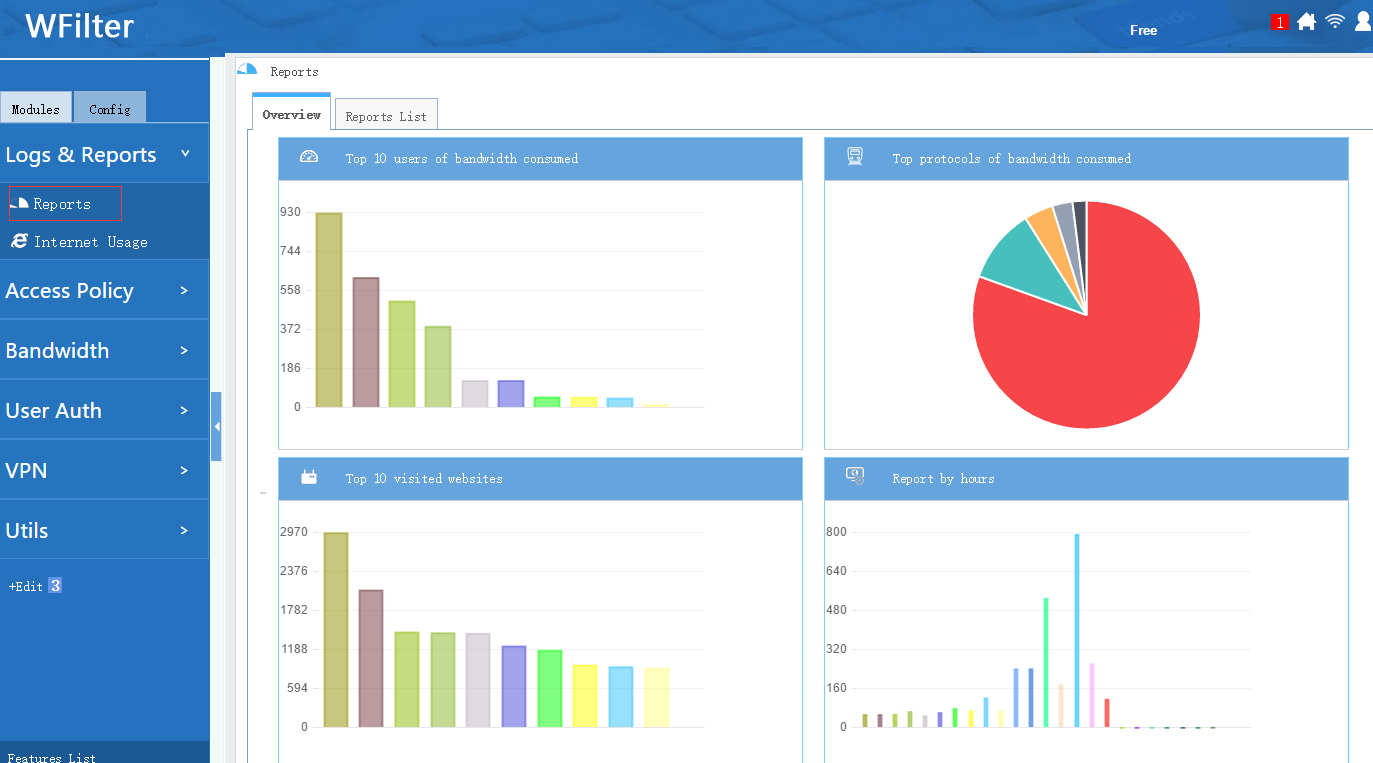
When deployed and configured properly, both WFilter ICF and WFilter NGF can block torrent completely. All torrent clients will have zero uploading and downloading speed.

![block_torrent04[1][2]](http://blog.wfilterngf.com/wp-content/uploads/2017/07/block_torrent0412.jpg)
WFilter ICF homepage: WFilter Internet Content Filter
WFilter NG homepage: WFilter NG firewall
WFilter videos: WFilter Videos





![block_torrent04[1][2]](http://blog.wfilterngf.com/wp-content/uploads/2017/07/block_torrent0412.jpg)